SOC 2 Readiness Assessment: Prepare for Your Audit
A SOC 2 readiness assessment is a structured evaluation of your organization's security controls, policies, and processes before the formal audit begins. Think of it as a practice run that identifies gaps, reduces surprises, and dramatically improves your chances of passing the actual SOC 2 audit on the first attempt.
Organizations that skip the readiness assessment often face extended audit timelines, unexpected findings, and costly remediation under time pressure. This guide walks you through exactly what a readiness assessment covers, how to run one, and what to expect at each stage.
Why a Readiness Assessment Matters
The numbers tell the story. Organizations that conduct a readiness assessment before their SOC 2 audit report 60% fewer findings during the formal examination. They also complete the audit process 4 to 8 weeks faster on average.
Here is what happens without one: your auditor arrives, starts testing controls, and discovers that your access review process exists on paper but has not been executed consistently. Or your change management policy references an approval workflow that was abandoned six months ago. These findings do not just delay the audit. They can result in qualified opinions or exceptions in your final report.
A readiness assessment catches these issues when you still have time to fix them.
Readiness Assessment vs. SOC 2 Audit: Key Differences
| Aspect | Readiness Assessment | SOC 2 Audit | |--------|---------------------|-------------| | Performed by | Internal team, consultant, or advisory firm | Licensed CPA firm | | Output | Gap analysis report with remediation plan | Formal SOC 2 report (Type I or Type II) | | Duration | 2-4 weeks | 4-12 weeks (Type II includes observation period) | | Cost | $10,000-$30,000 | $30,000-$150,000+ | | Regulatory standing | No formal attestation | AICPA-recognized attestation | | Repeat frequency | Before first audit, then as needed | Annually |
What the Assessment Covers

A thorough readiness assessment evaluates your organization against the SOC 2 Trust Service Criteria you plan to include in your audit scope. At minimum, every SOC 2 audit covers Security (Common Criteria). Most organizations also include Availability and Confidentiality.
1. Control Environment Review
The assessment starts with your control environment: the governance structure, policies, and organizational commitment to security that everything else rests on.
Evaluators examine:
- Board or executive oversight of security programs
- Organizational structure and reporting lines for security
- Code of conduct and ethics policies
- Risk management processes and risk appetite statements
- Commitment to competence (hiring, training, certifications)
Common gap: Many startups have informal security practices that work well but are not documented. The readiness assessment identifies where "we all know how this works" needs to become written policy.
2. Risk Assessment Process
SOC 2 requires a formal risk assessment process. The readiness evaluation checks whether you have:
- A documented risk assessment methodology
- Identified threats and vulnerabilities relevant to your services
- Assessed likelihood and impact of identified risks
- Mapped controls to identified risks
- A process for updating the risk assessment when the environment changes
Common gap: Organizations often perform a risk assessment once and never update it. SOC 2 expects this to be a living process, reviewed at least annually.
3. Information and Communication
This area covers how security-relevant information flows through your organization:
- Security policies are communicated to all employees
- Roles and responsibilities are clearly defined
- External communications about security commitments (SLAs, contracts, privacy notices)
- Incident notification processes for customers and regulators
4. Monitoring Activities
Evaluators check whether you actively monitor the effectiveness of your controls:
- Regular access reviews (quarterly for privileged access, semi-annually for standard)
- Vulnerability scanning and penetration testing schedules
- Log monitoring and alerting
- Vendor risk management reviews
- Internal audit or self-assessment activities
5. Control Activities (Technical and Administrative)
This is the bulk of the assessment. For each Trust Service Criteria in scope, evaluators test specific controls:
Logical access controls:
- Multi-factor authentication for production systems
- Role-based access control (RBAC) implementation
- Password policies and enforcement
- Privileged access management
- Access provisioning and deprovisioning procedures
Change management:
- Change request and approval workflows
- Separation of duties between development and production
- Code review requirements
- Testing before production deployment
- Emergency change procedures
Incident response:
- Documented incident response plan
- Defined roles and escalation paths
- Regular tabletop exercises or simulations
- Post-incident review process
Data protection:
- Encryption at rest and in transit
- Data classification scheme
- Data retention and disposal policies
- Backup and recovery procedures and testing
How to Run a Readiness Assessment
Option 1: Self-Assessment
Best for organizations with experienced security professionals on staff. Use the AICPA's Trust Service Criteria (available free on aicpa.org) as your checklist.
Pros: Lowest cost, builds internal knowledge, no external scheduling needed. Cons: Potential blind spots, no external validation, less credibility with stakeholders.
Option 2: Consultant-Led Assessment
Engage a security consulting firm (not your audit firm) to conduct the assessment.
Pros: External perspective catches blind spots, experienced assessors know common pitfalls, deliverables are typically more structured. Cons: Higher cost ($15,000-$30,000), requires vendor selection and scheduling.
Option 3: Platform-Assisted Assessment
Use a GRC platform like Vanta, Drata, or Secureframe that includes readiness assessment features. These platforms map your existing controls to SOC 2 criteria and highlight gaps automatically.
Pros: Fastest path to gap identification, continuous monitoring, evidence collection automation. Cons: Platform subscription cost, may not catch nuanced policy gaps, still need human review.
The Readiness Assessment Timeline
Here is a realistic timeline for a first-time SOC 2 readiness assessment:
Weeks 1-2: Scoping and Documentation Review
- Define Trust Service Criteria in scope
- Collect all policies, procedures, and system documentation
- Map your technology stack and data flows
Weeks 2-3: Control Testing
- Test technical controls (access management, encryption, logging)
- Review administrative controls (policies, training, vendor management)
- Interview process owners
Week 4: Gap Analysis and Reporting
- Compile findings with severity ratings
- Develop remediation recommendations with estimated effort
- Present findings to leadership
Weeks 5-16: Remediation
- Address critical and high-severity gaps first
- Update policies and procedures
- Implement missing technical controls
- Begin evidence collection for the audit period
Common Readiness Findings (and How to Fix Them)

Based on industry data, these are the most frequently identified gaps during SOC 2 readiness assessments:
1. Incomplete or Outdated Policies (Found in 78% of assessments)
The problem: Security policies exist but have not been reviewed in over a year, or key policies are missing entirely.
The fix: Conduct a policy review sprint. Prioritize: Information Security Policy, Acceptable Use Policy, Access Control Policy, Change Management Policy, Incident Response Plan, and Vendor Management Policy. Set annual review dates.
2. No Formal Risk Assessment (Found in 65% of assessments)
The problem: The organization has never conducted a formal risk assessment, or did one years ago that no longer reflects the current environment.
The fix: Use a framework like NIST SP 800-30 or ISO 27005 to conduct a risk assessment. Document methodology, identified risks, likelihood/impact ratings, and planned responses.
3. Inconsistent Access Reviews (Found in 72% of assessments)
The problem: Access reviews are supposed to happen quarterly but evidence shows they have been skipped or done inconsistently.
The fix: Automate access review workflows using your GRC platform or identity provider. Set calendar reminders. Document the results of every review, including the "no changes needed" reviews.
4. Missing Change Management Evidence (Found in 58% of assessments)
The problem: Changes are deployed to production without documented approval, testing evidence, or separation of duties.
The fix: Implement pull request requirements with mandatory reviews. Use deployment pipelines that enforce approval gates. Configure your CI/CD system to log every deployment with the approver's identity.
5. No Vendor Risk Management Program (Found in 61% of assessments)
The problem: Third-party vendors have access to sensitive data but no formal risk assessment or security review has been conducted.
The fix: Create a vendor inventory. Classify vendors by risk tier (based on data access and criticality). Collect SOC 2 reports or security questionnaires from high-risk vendors. Review annually.
What Comes After the Readiness Assessment
Once remediation is complete, you are ready to engage your audit firm. Here is the sequence:
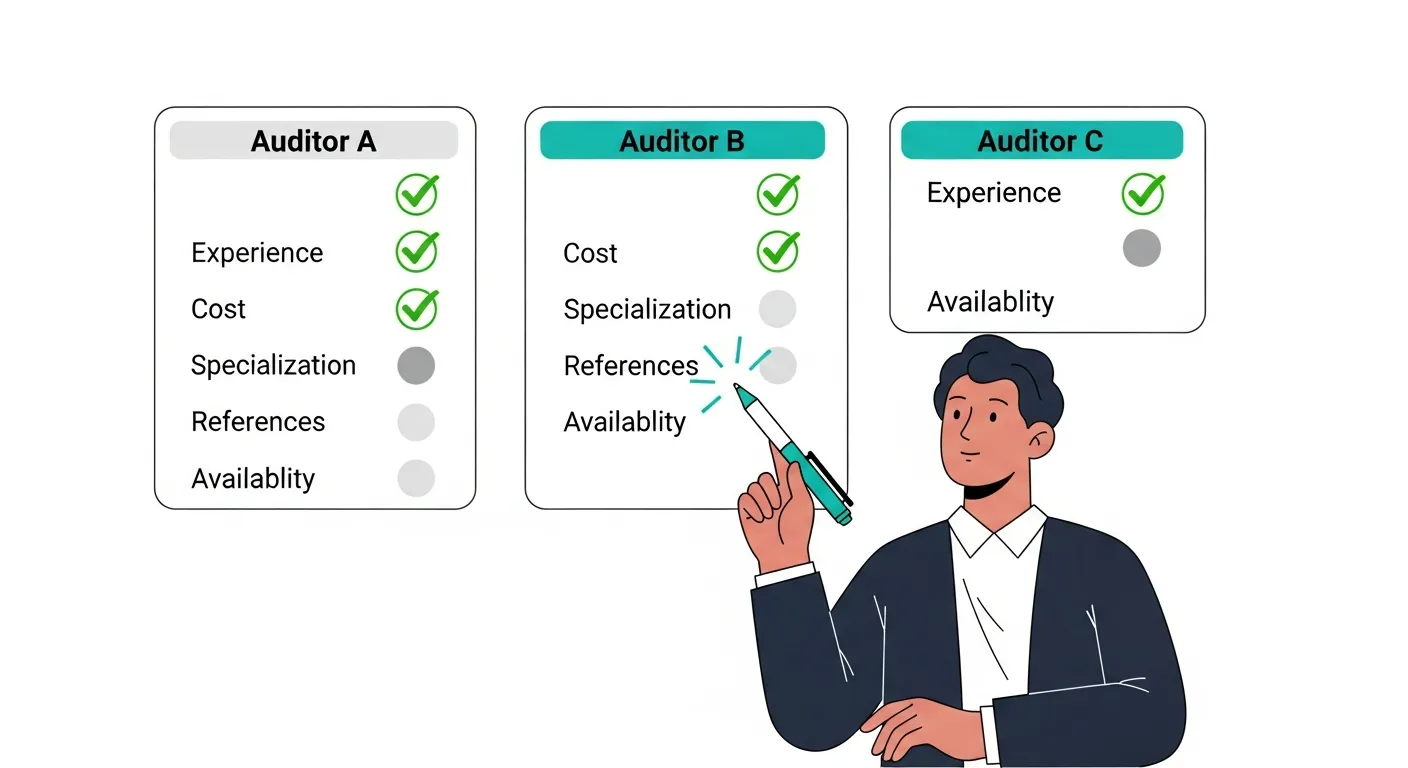
- Select your auditor (see our guide on how to choose a SOC 2 auditor)
- Define the audit scope with your auditor (Trust Service Criteria, system description, audit period)
- Begin the observation period (for Type II, typically 6 to 12 months)
- Collect evidence throughout the observation period
- Undergo fieldwork (auditor tests controls and reviews evidence)
- Receive and review the draft report
- Finalize the SOC 2 report
Frequently Asked Questions
How much does a SOC 2 readiness assessment cost?
A self-assessment costs primarily staff time, typically 80 to 160 hours of security team effort. Consultant-led assessments range from $10,000 to $30,000 depending on scope and organization size. GRC platform subscriptions that include readiness features run $10,000 to $50,000 per year. The investment is minor compared to the full SOC 2 audit cost.
Can the same firm do the readiness assessment and the audit?
Yes, but with restrictions. The AICPA allows advisory and attestation services by the same firm under certain conditions. The key requirement is that the firm cannot make management decisions for you. They can identify gaps and recommend solutions, but you must decide on and implement the remediation. Discuss independence requirements with your auditor before engaging them for advisory work.
How long is a SOC 2 readiness assessment valid?
There is no formal expiration, but a readiness assessment reflects a point in time. If significant changes occur after the assessment (new systems, organizational changes, updated policies), portions of the assessment may need to be repeated. Most organizations treat the assessment as valid for 6 to 12 months.
Do we need a readiness assessment every year?
Most organizations only need a formal readiness assessment before their first SOC 2 audit. After that, continuous monitoring through your GRC platform and internal audit activities serve the same purpose. However, if you are adding new Trust Service Criteria to your scope or have undergone major infrastructure changes, a targeted readiness assessment can be valuable.
What is the biggest mistake organizations make during readiness?
Treating it as a documentation exercise rather than an operational assessment. Having a beautiful access control policy means nothing if access reviews are not actually happening. The readiness assessment must test that controls are operating, not just that they exist on paper.