SOC 2 for SaaS Startups: Getting Compliant Fast
SOC 2 compliance has become the de facto security standard for SaaS companies selling to mid-market and enterprise customers. If your startup has ever lost a deal or stalled a procurement cycle because you could not produce a SOC 2 report, you already understand the business case. The question is not whether to get SOC 2 compliant, but how to do it without burning six months and six figures while you should be building product.
This guide is written specifically for SaaS startups with 10 to 200 employees. It covers the fastest path to your first SOC 2 report, realistic timelines and budgets, the tools that automate the heavy lifting, and the mistakes that derail early-stage companies.
Why SaaS Startups Need SOC 2
Three forces are driving SOC 2 adoption among SaaS companies:
Enterprise sales requirements. Over 80% of enterprise vendor security questionnaires now request a SOC 2 report. Without one, your deal sits in security review indefinitely, or the prospect moves to a competitor who already has one.
Investor expectations. Series A and B investors increasingly expect portfolio companies to have SOC 2 compliance in progress or completed. It signals operational maturity and reduces risk in the portfolio.
Customer trust. In a SaaS market where data breaches make weekly headlines, a SOC 2 report is tangible evidence that your company takes security seriously. It shortens sales cycles and reduces friction in security reviews.
SOC 2 Basics for Startup Founders
SOC 2 is an auditing framework developed by the American Institute of Certified Public Accountants (AICPA). It evaluates your organization against five Trust Service Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
Security (Common Criteria) is mandatory for every SOC 2 audit. The other four criteria are optional. Most SaaS startups include Security and Availability in their first audit, then add Confidentiality for the second cycle.
There are two report types:
- Type I: Evaluates control design at a single point in time. Faster to complete (4 to 8 weeks). Good for startups that need a report quickly.
- Type II: Evaluates control design and operating effectiveness over 3 to 12 months. The gold standard that enterprise buyers prefer.
Most startups begin with a Type I report to close immediate deals, then transition to Type II within 6 to 12 months.
The Fastest Path to SOC 2 for a Startup

Here is the accelerated timeline that well-prepared startups follow:
Weeks 1-2: Scoping and Gap Assessment
Define what is in scope for your audit. For a SaaS startup, this typically includes:
- Your production infrastructure (AWS, GCP, or Azure)
- Your application and its data stores
- Corporate IT systems (laptops, email, identity provider)
- People and processes (onboarding, offboarding, access reviews, incident response)
Run a readiness assessment to identify gaps between your current state and SOC 2 requirements. Common startup gaps include:
- No formal information security policy
- No documented risk assessment process
- Missing access review records
- No background check process for employees
- Incomplete vendor management program
- No business continuity or disaster recovery plan
Weeks 3-6: Remediation and Control Implementation
This is where most of the work happens. You need to:
Write policies. At minimum, you need an Information Security Policy, Acceptable Use Policy, Access Control Policy, Incident Response Plan, Change Management Policy, Risk Management Policy, Vendor Management Policy, and Business Continuity Plan. GRC platforms provide templates that you customize, not write from scratch.
Implement technical controls. Enable MFA for all systems. Configure encryption at rest and in transit. Set up centralized logging. Deploy endpoint protection. Enable automated vulnerability scanning. Configure backup systems with tested recovery procedures.
Establish operational processes. Schedule quarterly access reviews. Implement a change management workflow (pull requests with approvals). Set up onboarding and offboarding checklists. Document your incident response procedure. Conduct your first formal risk assessment.
Set up monitoring. Configure alerts for unauthorized access attempts, infrastructure changes, and security events. SOC 2 auditors will ask for evidence that your monitoring systems are active and reviewed.
Weeks 7-8: Type I Audit (or Begin Type II Observation)
Engage a CPA firm and begin the audit. For a Type I:
- The auditor reviews your control documentation and evidence
- They test whether controls are designed properly and in place
- They issue a report within 2 to 4 weeks of completing fieldwork
For startups going directly to Type II, weeks 7 onward become the observation period where you operate your controls consistently while collecting evidence.
What SOC 2 Costs a Startup
Budget realistically. Here is what startups in the 10 to 200 employee range typically spend:
| Cost Category | Range | Notes | |--------------|-------|-------| | GRC platform | $10,000 - $30,000/year | Vanta, Drata, Secureframe, or Thoropass | | Auditor fees (Type I) | $15,000 - $40,000 | First-time startup audit | | Auditor fees (Type II) | $30,000 - $80,000 | 6-month observation, 50-200 employee scope | | Internal labor | 80 - 200 hours | Spread across engineering, IT, and operations | | Policy development | $0 - $10,000 | Free with GRC platform templates, or consultant | | Penetration test | $5,000 - $20,000 | Not required for SOC 2 but recommended | | Total (Year 1, Type I) | $30,000 - $80,000 | Including platform and audit | | Total (Year 1, Type II) | $50,000 - $140,000 | Including platform, observation period, and audit |
Choosing a GRC Platform
Compliance automation platforms have transformed SOC 2 for startups. Instead of managing evidence collection manually (screenshots, spreadsheets, email threads), these platforms integrate directly with your cloud infrastructure, identity provider, and HR systems to collect evidence automatically.
The three dominant platforms for startups are Vanta, Drata, and Secureframe. All three offer:
- Automated evidence collection from AWS, GCP, Azure, Okta, Google Workspace, GitHub, and dozens of other integrations
- Policy templates customizable to your organization
- Continuous monitoring with alerts for control failures
- Auditor portals that streamline the audit process
- Employee security training modules
How to choose: Request demos from at least two platforms. Evaluate based on:
- Integration coverage. Does the platform connect to your specific tech stack? Check for native integrations with your cloud provider, identity provider, CI/CD pipeline, and HR system.
- Auditor partnerships. Most platforms have preferred auditor networks with pre-negotiated rates. Ask about these partnerships since they can save $5,000 to $15,000 on audit fees.
- Time to value. Ask each vendor how long it takes for a startup similar to your size and stack to go from signup to audit-ready. Get references from comparable customers.
- Pricing model. Some platforms charge per employee, others by feature tier. Model the costs at your current headcount and at 2x your current headcount.
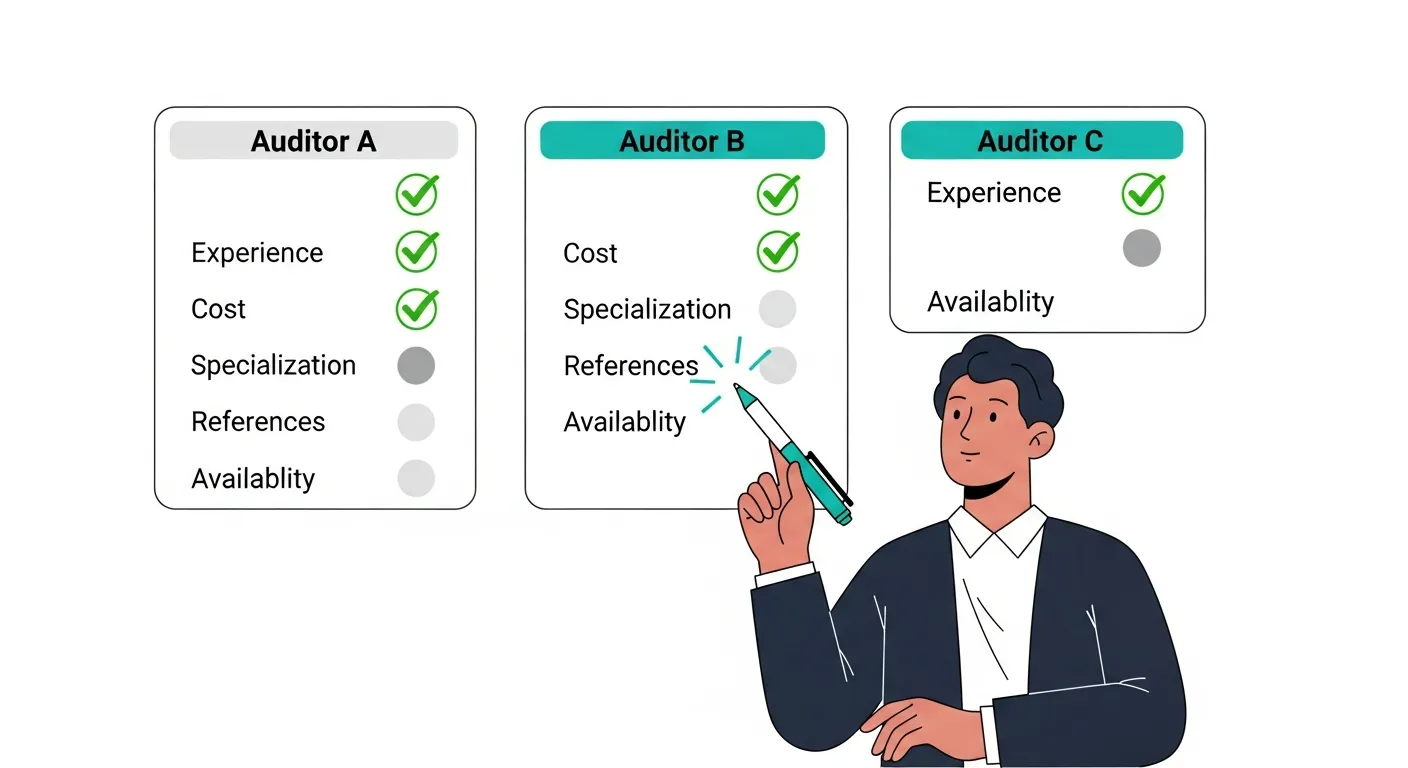
Choosing a SOC 2 Auditor

Your auditor must be a licensed CPA firm. Beyond that baseline requirement, consider:
Experience with startups. Firms that specialize in startup and technology company audits understand cloud-native architectures and modern development practices. They will not ask irrelevant questions about physical server rooms when your infrastructure runs entirely on AWS.
Experience with your GRC platform. Auditors who have worked with Vanta, Drata, or Secureframe before can pull evidence directly from the platform, reducing back-and-forth and accelerating the engagement.
Scope and pricing. Get quotes from at least two firms. Audit fees vary significantly based on the firm's size, location, and demand. Smaller boutique firms often offer competitive rates for startups.
Timeline commitments. Ask for a specific timeline with milestones. An auditor who cannot commit to a completion date may not have the bandwidth to prioritize your engagement.
For a deeper comparison, see our guide on how to choose a SOC 2 auditor.
Common Mistakes SaaS Startups Make
Scoping Too Broadly
Including every system in your SOC 2 scope adds cost and complexity without proportional benefit. Your production SaaS platform, its supporting infrastructure, and the people and processes that manage it are the core scope. Internal marketing tools, personal devices used for non-sensitive work, and experimental development environments can often be excluded.
Starting Too Late
"We will do SOC 2 when we need it" is a common refrain that turns into a scramble when a high-value prospect sends a security questionnaire with a 30-day deadline. Start at least 6 months before you expect enterprise pipeline to materialize.
Underestimating Internal Labor
Even with a GRC platform handling automation, someone on your team needs to write policies, configure integrations, remediate gaps, and coordinate with the auditor. Budget 80 to 200 hours of internal effort for a first-time audit.
Treating SOC 2 as a One-Time Project
SOC 2 is an ongoing program, not a one-time project. After your initial report, you need to maintain controls, collect evidence continuously, and undergo annual audits. Build compliance into your operational rhythm, not as a separate initiative.
Not Involving Engineering Early
Engineering teams own many of the technical controls that SOC 2 evaluates: code review processes, deployment pipelines, access management, logging, and encryption. Involve your engineering lead from week one to ensure buy-in and realistic implementation timelines.
What Enterprise Buyers Actually Look For
Understanding how enterprise security teams evaluate your SOC 2 report helps you prepare:
Unqualified opinion. The auditor's opinion should be "unqualified" (clean), meaning no material issues were found. A qualified opinion with exceptions may be acceptable if the exceptions are immaterial, but it raises questions.
Scope coverage. Buyers check that the audit scope covers the services they are evaluating. If your SOC 2 report covers only a legacy product and not the new platform they are purchasing, it does not satisfy their requirements.
Trust Service Criteria. Security is expected. Availability is strongly preferred for SaaS companies. Confidentiality adds further assurance for data-sensitive industries.
Observation period. For Type II, a 6-month minimum observation period is the practical baseline. A 3-month period, while technically valid, may draw questions from security teams.
Recency. Reports should be less than 12 months old. Ideally, provide the most recent report plus a bridge letter covering the gap between the report period and the current date.
SOC 2 and Other Compliance Frameworks

SOC 2 is often the starting point, but it is rarely the only compliance requirement SaaS startups encounter.
ISO 27001: An international security management system standard. Many enterprise buyers in Europe and Asia require ISO 27001 in addition to or instead of SOC 2. There is significant overlap, roughly 60% to 70% of controls are shared between SOC 2 and ISO 27001.
HIPAA: Required if your SaaS product handles protected health information. HIPAA compliance is separate from SOC 2 but can be addressed in the same audit cycle with proper planning.
PCI DSS: Required if your application processes, stores, or transmits credit card data. PCI DSS has its own audit framework and certification body.
NIST CSF: The NIST Cybersecurity Framework is widely used as a reference but is voluntary for most private companies. Government contractors may need NIST 800-171 compliance.
Your 90-Day SOC 2 Action Plan
Days 1-7: Select and onboard a GRC platform. Connect your cloud infrastructure, identity provider, and HR system.
Days 8-14: Run the platform's automated readiness assessment. Categorize gaps by severity and effort.
Days 15-30: Write and adopt core policies using platform templates. Implement critical technical controls (MFA, encryption, logging).
Days 31-45: Complete remaining remediation items. Configure automated evidence collection for all in-scope systems.
Days 46-60: Engage an auditor. Provide access to your GRC platform for evidence review.
Days 61-75: Support auditor fieldwork. Answer questions, provide supplemental evidence, resolve any findings.
Days 76-90: Receive your SOC 2 Type I report. Begin the Type II observation period for the next cycle.
Frequently Asked Questions
How long does SOC 2 take for a startup?
A well-prepared startup can complete a Type I audit in 8 to 12 weeks from the decision to start. This includes 4 to 6 weeks of preparation and remediation, plus 2 to 4 weeks of audit fieldwork. Type II requires an additional 3 to 12 month observation period.
Can a 10-person startup pass SOC 2?
Yes. SOC 2 controls scale with organizational complexity. A 10-person company needs simpler processes than a 500-person enterprise. The key requirements (access controls, encryption, monitoring, incident response) apply regardless of size, but the implementation can be appropriately lightweight.
Do we need a dedicated compliance hire?
Not for your first audit. Most startups designate an existing team member (often a senior engineer, Head of IT, or COO) as the compliance lead. A GRC platform handles most of the ongoing work. A dedicated compliance hire becomes valuable at 100 to 200 employees or when managing multiple compliance frameworks.
Is SOC 2 certification required by law?
No. SOC 2 is a voluntary framework. However, it is effectively mandatory for SaaS companies selling to enterprises because those buyers require it as a condition of doing business. Think of it as market-driven rather than regulation-driven.
What happens if we fail the SOC 2 audit?
You do not technically "fail" a SOC 2 audit. The auditor issues a report with their opinion. If significant control deficiencies exist, the auditor may issue a qualified opinion or note exceptions. You can address the findings, remediate, and undergo a new audit. The failed report is not published anywhere public.