ISO 27001 Internal Audit: Checklist and Requirements for 2026
An ISO 27001 internal audit is a required self-assessment that verifies your Information Security Management System (ISMS) conforms to the ISO/IEC 27001:2022 standard before a certification body ever walks through the door. Clause 9.2 of the standard makes internal audits mandatory, and failure to run them properly is one of the most common reasons organizations receive nonconformities during their external certification audit.
If you are preparing for certification or maintaining it across the three-year cycle, this guide walks through the internal audit requirements, a usable 40-point checklist, who can conduct the audit, what findings are acceptable, and how to write an audit report that holds up under external scrutiny.
What Is an ISO 27001 Internal Audit?
An ISO 27001 internal audit is a systematic, independent examination of your ISMS to confirm that it meets the requirements of ISO 27001 and the organization's own documented policies. The audit covers both the management system clauses (4 through 10) and the applicable Annex A controls listed in your Statement of Applicability.
Internal audits serve three purposes. They surface nonconformities before the external audit. They feed management reviews with evidence of how controls are performing. They also demonstrate to the certification body that your ISMS has a functioning self-correction loop, which is a core expectation of any ISO management system standard.
The scope of an internal audit covers every area of the ISMS at some point within the audit program, but a single audit session does not have to cover everything at once. Most organizations split the work across multiple audits throughout the year, following a defined audit plan.
When Are ISO 27001 Internal Audits Required?
ISO 27001 requires internal audits at "planned intervals," a phrase that allows flexibility but still imposes a practical floor. In practice, most certification bodies expect to see:
- At least one full ISMS audit per year covering all clauses and applicable controls over a defined cycle (typically one, two, or three years)
- A completed audit before the initial certification audit (Stage 1 and Stage 2)
- A completed audit before each annual surveillance visit
- Focused audits on high-risk areas more frequently than the main cycle
The ISO 27001 certification cycle runs three years. The internal audit program should be structured so that every clause and every applicable Annex A control is audited at least once within that three-year window. If your risk landscape includes high-impact areas, such as cloud infrastructure, payment processing, or personal health data, those should be audited annually at a minimum.
A common mistake is treating the internal audit as a one-time exercise before certification. The ISO 27001 standard is explicit that the audit program must be ongoing.
Who Can Perform an ISO 27001 Internal Audit?

Clause 9.2.2 requires that auditors be objective and impartial. They cannot audit their own work. In practice, this means:
- Internal staff from a different team. An IT manager can audit HR controls, but cannot audit the IT controls they own.
- A separate internal audit function. Larger organizations have dedicated internal auditors who sit outside operational teams.
- An external consultant. Small organizations often hire a third-party consultant to run the internal audit because they lack the staff count to maintain independence.
The auditor does not need to hold a specific certification to be valid under ISO 27001, but most organizations require their internal auditors to complete ISO 27001 Lead Auditor or Internal Auditor training. The PECB, BSI, and IRCA-certified training programs are the most widely recognized.
For startups under 20 employees, outsourcing the internal audit to a consultant is usually the cleanest path. It takes roughly three to five business days of consultant time for a first-year audit and two to three days for maintenance audits. Cost runs between $4,000 and $12,000 depending on scope.
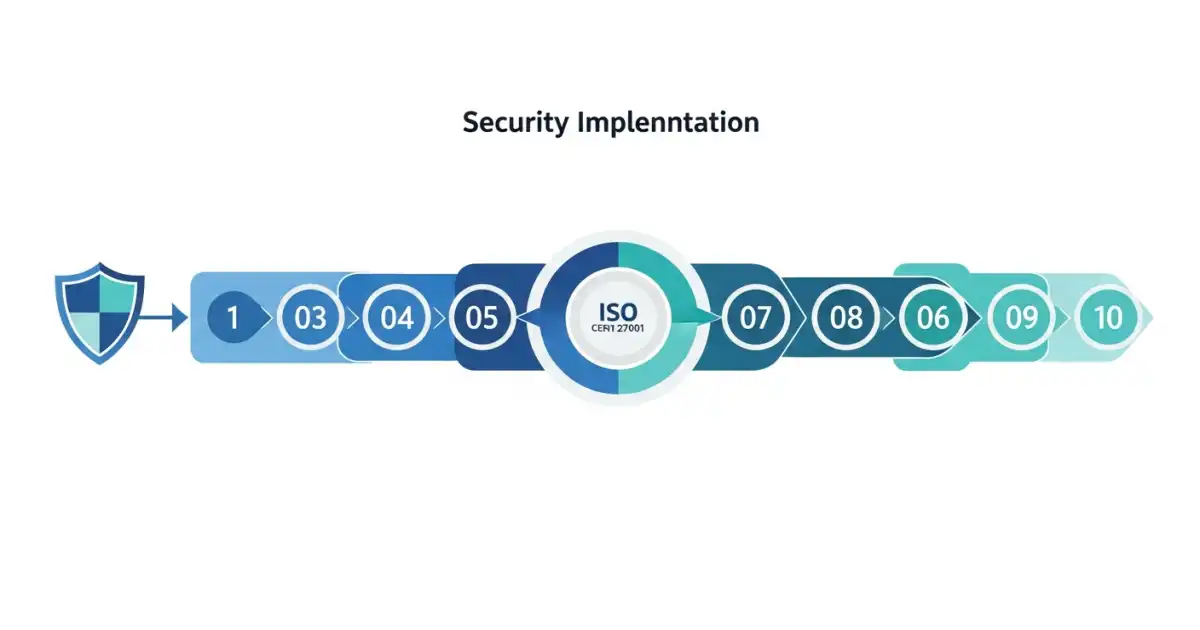
ISO 27001 Internal Audit Process: 6 Phases
A defensible internal audit follows a repeatable six-phase process. Each phase has documented outputs that become evidence for the external audit.
Phase 1: Audit Planning
Define the scope, objectives, criteria, and timeline. The audit plan should identify which clauses and controls are in scope for this specific audit, which departments and sites will be audited, the audit team, and the reporting schedule. A typical plan runs one page per audit session.
Phase 2: Document Review
Before interviewing anyone, the auditor reviews the ISMS documentation. This includes the Statement of Applicability, risk treatment plan, policies, procedures, and records of previous audits, management reviews, and corrective actions. Missing, outdated, or contradictory documents are logged as potential findings.
Phase 3: Fieldwork
The auditor conducts interviews with control owners, observes processes, and samples records. Each Annex A control selected for the audit needs at least one piece of sampled evidence. For access control, that might be a sample of five user access reviews. For supplier management, a sample of three supplier risk assessments.
Phase 4: Analysis
The auditor compares what they observed against the ISO 27001 requirements and the organization's own documented policies. Gaps fall into three categories: major nonconformity, minor nonconformity, and opportunity for improvement.
Phase 5: Reporting
The internal audit report documents scope, findings, evidence, and recommendations. Each finding references the specific clause or control, the evidence reviewed, and the gap identified. A complete report is typically 10 to 25 pages for a medium-sized ISMS.
Phase 6: Follow-up
Findings feed the corrective action process. The audit is not closed until every major nonconformity has a documented root cause analysis, corrective action, and verification that the action worked. Minor nonconformities require corrective action but not always a root cause analysis.
ISO 27001 Internal Audit Checklist: 40 Items
Use this checklist as a starting point for any internal audit. Adapt it to your specific Statement of Applicability. Items are organized by clause and by Annex A domain.
Clauses 4-10 (Management System)
- Is the scope of the ISMS documented and current?
- Does the ISMS scope match what appears in the Statement of Applicability?
- Are interested parties and their requirements documented?
- Is the information security policy approved by top management and communicated?
- Are information security objectives documented, measurable, and tracked?
- Is the risk assessment methodology documented and consistent?
- Is the risk treatment plan complete, with owners and due dates?
- Is the Statement of Applicability current and aligned with the latest Annex A controls?
- Are resources for the ISMS documented and adequate?
- Are competence records (training, certifications) maintained for ISMS roles?
- Is the communication plan for security matters documented?
- Are documented information controls (version, approval, distribution) followed?
- Are operational planning records available for security processes?
- Is evidence of risk assessments and risk treatment up to date?
- Is a monitoring and measurement plan in place and generating records?
- Are internal audits conducted at planned intervals?
- Is top management conducting documented management reviews?
- Are nonconformities and corrective actions tracked to closure?
- Is there evidence of continual improvement?
Annex A Controls (Samples)
- A.5.1 Policies: Are all required policies approved, dated, and reviewed annually?
- A.5.2 Roles and responsibilities: Is a security responsibility matrix maintained?
- A.5.9 Inventory of assets: Is the asset register current and owned?
- A.5.15 Access control: Are user access reviews conducted at defined intervals?
- A.5.23 Cloud services: Are cloud service risk assessments documented?
- A.5.30 ICT readiness: Are business continuity and disaster recovery tests documented?
- A.5.34 Privacy: Is a privacy impact assessment process in place?
- A.6.3 Awareness training: Is security training delivered and tracked?
- A.6.7 Remote working: Is a remote working policy documented and enforced?
- A.7.4 Physical security monitoring: Are visitor logs, badge records, and CCTV retained?
- A.8.1 User endpoint devices: Is an endpoint security baseline documented and monitored?
- A.8.5 Secure authentication: Is MFA enforced on all privileged accounts?
- A.8.7 Protection against malware: Are endpoint protection logs reviewed?
- A.8.8 Technical vulnerability management: Are vulnerability scans run and remediated on schedule?
- A.8.12 Data leakage prevention: Are DLP controls documented for sensitive data flows?
- A.8.16 Monitoring: Are SIEM logs retained for the documented period?
- A.8.24 Cryptography: Is cryptographic key management documented?
- A.8.28 Secure coding: Are secure coding standards followed and reviewed?
- A.8.32 Change management: Are changes authorized, tested, and logged?
- A.8.33 Test information: Is production data masked in non-production environments?
- Supplier audit: Has the top-tier supplier list been reviewed for security obligations?
Common ISO 27001 Internal Audit Findings

After reviewing hundreds of internal audit reports, the same findings appear repeatedly. Fixing these before the external audit saves significant time and money.
| Finding | Frequency | Typical Cause | |---|---|---| | Outdated Statement of Applicability | Very high | Annex A 2022 revision not incorporated | | Access review evidence missing for 1+ quarters | Very high | No calendared review cycle | | Supplier risk assessments not done for new vendors | High | No onboarding checkpoint | | Security training completion below 100% | High | New hires missed in rollout | | Risk treatment plan overdue on 1+ items | High | No automated tracking | | Vulnerability remediation SLAs exceeded | Medium | Patch backlog, no escalation | | Missing management review minutes | Medium | Informal discussions not documented | | Incident log not reviewed quarterly | Medium | No defined review cadence | | Backup restoration tests not performed | Medium | Assumed working, never verified |
How Long Does an ISO 27001 Internal Audit Take?
For a small organization (under 50 employees) running the full ISMS through a first-year audit, expect:
- Planning: 1-2 days
- Document review: 2-3 days
- Fieldwork: 3-5 days
- Reporting: 2-3 days
- Total: 8-13 days of auditor effort, spread across 3-4 calendar weeks
Mid-size organizations (50 to 500 employees) typically run 15 to 25 days per full audit. Enterprise programs run multiple focused audits throughout the year totaling 40 to 80 days.
Maintenance audits after the first year drop by 30 to 40 percent because documentation is already established and the auditor already knows the environment.
ISO 27001 Internal Audit Report Template
A complete internal audit report includes ten sections:
- Executive summary (half a page) with the audit objective, scope, and headline findings
- Audit plan reference including the dates, auditor names, and approved scope
- Scope and exclusions listing what was covered and what was deliberately out of scope
- Audit methodology explaining sampling approach, evidence types, and interview schedule
- Clause-by-clause findings with evidence citations
- Annex A control findings organized by domain
- Nonconformities log classified as major or minor with clause references
- Opportunities for improvement (not nonconformities, but recommendations)
- Corrective action requests with owners and due dates
- Appendices including interview list, documents reviewed, and sampling evidence
External auditors read the internal audit report carefully. A thin, vague internal audit report is a signal that the ISMS itself is thin and vague.
Integrating Internal Audit with Other Compliance Work

For organizations that hold multiple certifications, the internal audit program should be integrated rather than run in parallel. Many ISO 27001 Annex A controls map directly to SOC 2 Trust Service Criteria. Auditing them once with both frameworks in mind cuts the total effort significantly.
The same integration works for HIPAA risk assessments, PCI DSS control reviews, and NIST CSF self-assessments. Build the control mapping once and reuse evidence across frameworks. The NIST CSF and ISO 27001 comparison highlights the overlap for organizations running both.
ISO 27001 Internal Audit Cost
Typical cost ranges for a first-year internal audit:
| Organization Size | Outsourced | In-house (staff time) | |---|---|---| | 1-50 employees | $4,000-$8,000 | 1 FTE for 2 weeks | | 51-250 employees | $8,000-$18,000 | 1 FTE for 4 weeks | | 251-1000 employees | $15,000-$35,000 | 2 FTE for 6 weeks | | 1000+ employees | $30,000-$100,000+ | Dedicated internal audit team |
Follow-up audits in subsequent years typically run 60 to 75 percent of the first-year cost because documentation and auditor familiarity reduce effort.
Frequently Asked Questions
Is an ISO 27001 internal audit required every year?
Yes, in practice. The standard says "planned intervals" but certification bodies expect at least one full audit per year, structured so that every clause and applicable control is audited within a defined cycle (usually one to three years).
Can I use internal audit software instead of spreadsheets?
Yes. Compliance automation platforms like Vanta, Drata, Secureframe, Sprinto, and Tugboat Logic include internal audit modules that manage sampling, evidence collection, and reporting. For small organizations, a disciplined spreadsheet works. Automation becomes valuable once you have more than 40 controls or multiple frameworks.
What happens if the internal audit finds a major nonconformity?
Major nonconformities must be addressed before the external audit closes. For an initial certification, an open major nonconformity can result in certification being withheld until the finding is resolved. Fix it, document the corrective action, and verify effectiveness with a follow-up audit.
Can the CISO conduct the internal audit?
The CISO can conduct the audit of areas they do not own, such as HR or finance controls. They cannot audit the security controls they are responsible for. Most organizations either hire a consultant or rotate audit responsibilities so that no one audits their own work.
How does the internal audit differ from the external certification audit?
The internal audit is conducted by the organization or a consultant working on its behalf. The external audit is conducted by an accredited certification body. Internal audits can be scoped flexibly, while the external audit must cover the full certified scope. Findings in an internal audit do not jeopardize certification directly, but unresolved findings will.
How many samples should the auditor pull for each control?
There is no fixed rule. A common approach is the square root of the population plus one, capped at 25 for large populations. For 100 user access reviews, sample 11. For 10,000 change tickets, sample 25. Document the sampling basis in the audit plan.
Do I need to audit controls that are marked "not applicable" in the SoA?
No. Controls excluded in the Statement of Applicability are out of scope for the audit. However, the decision to exclude them is in scope. The auditor should confirm that the exclusion justification in the SoA is still accurate.
How soon after the internal audit should the external audit happen?
Ideally within three to six months. If the gap is longer, the certification body may question whether the audit evidence is still representative of current operations. If the gap is shorter than one month, there may not be enough time to close findings and implement corrective actions.
About the Author
James Mitchell is a Compliance and Security Analyst with over 8 years of experience helping organizations prepare for ISO 27001, SOC 2, and HIPAA audits. He has led internal audits for SaaS companies from pre-seed through Series C and has managed ISMS programs through multiple surveillance cycles. He writes for Security Compliance Guide to help compliance teams ship defensible audits without the guesswork.
Related reading:
- ISO 27001 Annex A Controls: Full List Explained
- ISO 27001 Certification Cost: Breakdown by Company Size
- ISO 27001 Audit Process: Stage 1 and Stage 2 Explained
- NIST CSF vs ISO 27001: Detailed Comparison
External reference: ISO/IEC 27001:2022 Information security management systems. See the official ISO standards page for the current version of the standard.