Zero Trust Architecture: 2026 Complete Guide
Zero Trust Architecture (ZTA) is a security model that treats every user, device, and network request as untrusted by default and forces explicit verification before any resource access is granted. The authoritative definition lives in NIST SP 800-207, the federal publication that turned a marketing phrase into an engineering blueprint.
This guide is written for CISOs, security architects, IT directors, and the engineering leads who actually have to make Zero Trust work on a Tuesday. It covers what NIST actually says, the seven tenets, the policy components, real cost and timeline ranges, how ZTA compares to a traditional perimeter model, and where most rollouts go wrong.
The reader is assumed to have read at least one vendor explainer already. We will not repeat the castle-and-moat metaphor. We will tell you what NIST 800-207 requires, how the CISA Zero Trust Maturity Model phases the work, and what a credible 18-month rollout looks like at a 2,000-employee company.
For the deeper dive into the federal standard, see our NIST 800-207 implementation guide. For the controls catalog that operationalizes most ZTA components, see NIST 800-53. For a broader compliance map, see the cybersecurity compliance guide.
What is Zero Trust Architecture?
Zero Trust Architecture is the federal term for a security design where trust is never granted implicitly based on network location. NIST SP 800-207 defines it as "an evolving set of cybersecurity paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources". In plain language: it does not matter whether a request comes from inside the corporate LAN, a coffee shop, or a partner network. Every request is evaluated on its own merits, every time.
The model rests on seven tenets from NIST SP 800-207:
- All data sources and computing services are treated as resources.
- All communication is secured regardless of network location.
- Access is granted on a per-session basis.
- Access is determined by dynamic policy that includes the observable state of the requester.
- The enterprise monitors the integrity and security posture of all assets.
- Authentication and authorization are dynamic and strictly enforced before access.
- The enterprise collects telemetry on assets, infrastructure, and communications and uses it to improve posture.
The tenets are design principles, not a checklist. A real ZTA is the set of identity systems, device posture engines, segmentation, access proxies, and data controls that together satisfy them for every resource.
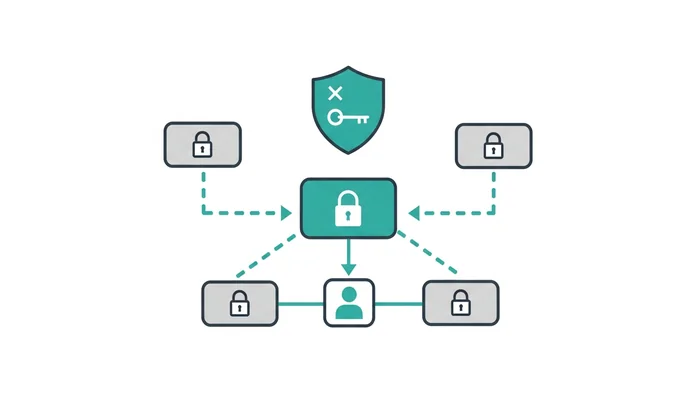
The model also names three logical components:
- Policy Engine (PE): the brain. Takes signals (identity, device health, behavior, threat intelligence) and outputs an access decision.
- Policy Administrator (PA): the executor. Establishes or tears down the session based on the PE's decision.
- Policy Enforcement Point (PEP): the gatekeeper. Sits inline with the resource and either passes or blocks the request.
Whether the resource is an SSH server, a SaaS app, a database, a Kubernetes pod, or a network segment is irrelevant to the model.
Why Zero Trust matters in 2026

The perimeter model has been dead for a decade and the breach data finally caught up with the architects.
Three forces moved Zero Trust from buzzword to mandate:
Federal direction. Executive Order 14028, signed May 2021, directed federal civilian agencies to adopt Zero Trust. The follow-on OMB Memorandum M-22-09 set deadlines across identity, device, network, application, and data pillars. The DoD Zero Trust Reference Architecture extended this to defense systems with a 2027 target. When the federal government writes a deadline, the contractor ecosystem follows.
Breach economics. Stolen credentials have been a top attack vector for over a decade. A perimeter model assumes attackers stay outside; the breach data says they walk in with valid credentials and pivot laterally. Zero Trust removes lateral movement because every internal hop requires its own authorization.
The hybrid workforce. Most security teams no longer manage a network. They manage identity, devices, and access across hundreds of SaaS applications, a few cloud providers, and a residual data center. The NIST Cybersecurity Framework 2.0 now references Zero Trust directly in its Protect function. CISA's Zero Trust Maturity Model v2.0 provides a phased path across five pillars.
The cost of a credential-based intrusion that pivots inside a flat network for 30 days is routinely 8 figures. The cost of a phased Zero Trust rollout is materially less.
Zero Trust requirements and the five pillars
NIST defines the architecture. CISA's Zero Trust Maturity Model operationalizes it into five pillars, each scored across four maturity stages (Traditional, Initial, Advanced, Optimal). The five pillars are the practical scope of any rollout.
| Pillar | What it covers | Optimal-stage indicators |
|---|---|---|
| Identity | Authentication, authorization, identity stores, privilege management | Phishing-resistant MFA everywhere, continuous validation, just-in-time access for privileged actions |
| Devices | Inventory, posture assessment, endpoint detection, patch state | Real-time posture as an access input, automatic isolation of non-compliant endpoints |
| Networks | Segmentation, encryption in transit, traffic visibility | Microsegmentation around every workload, all traffic encrypted, full east-west visibility |
| Applications and Workloads | Application access, secure development, workload identity | Continuous authorization per API call, secrets rotated automatically, workload identity tied to attestation |
| Data | Classification, encryption, data loss prevention, rights management | Tagged data everywhere, encryption keyed to identity, access decisions include data sensitivity |
Most enterprises start at Traditional or Initial across all five pillars. Reaching Advanced across the board is a 24 to 36 month journey at a typical 2,000-employee company. Optimal is a multi-year program that few organizations actually complete; the public sector targets it because executive orders require it.
Two cross-cutting capabilities support the pillars: visibility and analytics, and automation and orchestration. Without those, the pillars produce a more expensive version of the legacy architecture with a fresh coat of vendor paint.
Most ZTA controls map directly to control families in NIST SP 800-53: Access Control (AC), Identification and Authentication (IA), Audit and Accountability (AU), and System and Communications Protection (SC). If you already run a NIST 800-53 or NIST 800-171 program, 60 to 70% of your ZTA controls are already specified. They need to be re-architected around per-request decisioning, not perimeter trust.
Zero Trust Architecture cost and timeline
Zero Trust costs scale with company size, application portfolio, and how much legacy network has to be retired. For a representative 2,000-employee company with mixed on-prem and cloud, a credible 2026 budget looks like:
- Identity stack upgrade: $200K to $800K for phishing-resistant MFA, modern IdP (Okta, Entra ID, Ping), and a privileged access management platform.
- Endpoint and device posture: $150K to $500K annually for EDR, MDM, and posture-as-a-signal integration.
- ZTNA (Zero Trust Network Access): $100K to $400K annually for a ZTNA platform (Cloudflare Access, Zscaler ZPA, Netskope, Palo Alto Prisma Access, Tailscale).
- Microsegmentation: $200K to $1M for east-west segmentation tooling (Illumio, Akamai Guardicore, native cloud constructs).
- Internal program: $500K to $1.5M for a director-level lead, two architects, and a PM for the 18-month rollout.
- External advisory: $200K to $700K for a systems integrator in year one.
Total year-one cost for a mid-market enterprise: $1.5M to $4M, settling at $1M to $2.5M annually in steady state.
A representative 18-month rollout:
- Months 1-3: Discovery and scoping. Identify protect surfaces, map access flows, baseline against the CISA model.
- Months 3-6: Identity foundation. Phishing-resistant MFA everywhere, PAM deployed, IdP modernized.
- Months 6-9: Device posture and ZTNA. EDR-to-Policy-Engine integration live, ZTNA fronts the top 20 apps, VPN scope reduced.
- Months 9-15: Microsegmentation and workload identity. East-west segmentation, workload identity for production, secrets management consolidated.
- Months 15-18: Data layer. Classification, DLP integration with access decisions, analytics pipeline tuned.
Companies that try to compress this into 6 months end up with a vendor product, not an architecture.
Zero Trust process: the standard 8-step workflow

Every Zero Trust rollout, whether at a 200-person startup or a 200,000-person bank, follows a similar workflow. The terminology varies. The order does not.
Step 1. Identify the protect surface. List the resources whose compromise would actually hurt the business: customer data stores, source code, financial systems, admin consoles, production secrets. The protect surface is always smaller than the attack surface. Design starts there.
Step 2. Map the transaction flows. For each protect-surface resource, document who accesses it, from where, with what device, and what they do with it. The map will be incomplete in year one. Instrument the rest, revisit quarterly.
Step 3. Architect the environment. Place a PEP in front of each protect-surface resource. Decide which PEP technology fits: identity-aware proxy, ZTNA broker, service mesh, microsegmentation gateway, API gateway. Most enterprises end up with three to five PEP technologies.
Step 4. Write the policy. For each resource, define what the Policy Engine evaluates: who, what, when, where, why. Start coarse (role-based) and refine toward attribute-based decisions over time.
Step 5. Implement the Policy Engine. Consolidate signals: identity from the IdP, device posture from EDR, threat intelligence, behavior analytics. Most enterprises use their IdP as the foundational PE.
Step 6. Pilot and migrate. Pick three to five high-value applications and front them with the new PEPs. Migrate users in phases. Keep VPN running in parallel until pilots stabilize.
Step 7. Monitor and adapt. Instrument every access decision. Build dashboards for denied access by resource, user, and reason. Tune policy to reduce false positives.
Step 8. Expand the protect surface. Add the next tranche of resources. Retire legacy perimeter controls. Re-baseline against the CISA model annually.
Zero Trust is an operating model, not a project. Treat it as a project and the work piles up in years two and three.
Zero Trust vs related frameworks
Zero Trust overlaps with, but does not replace, several adjacent frameworks. Understanding the relationships avoids duplicate work.
Zero Trust vs SASE. Secure Access Service Edge (SASE) is a converged network and security edge, usually from a single vendor. Zero Trust is the architectural philosophy. ZTNA is one component of a SASE offering, alongside SWG, CASB, FWaaS, and SD-WAN. Most enterprises end up with SASE as the delivery vehicle for the network-layer pieces of their ZTA.
Zero Trust vs the NIST Cybersecurity Framework. The NIST Cybersecurity Framework 2.0 has six functions: Govern, Identify, Protect, Detect, Respond, Recover. Zero Trust lives primarily inside Protect, with overlap into Identify and Detect. CSF tells you what outcomes matter; ZTA tells you how to design the access layer to deliver them.
Zero Trust vs NIST 800-53. NIST SP 800-53 is the control catalog. ZTA is the architecture. The AC, IA, and SC control families specify what a ZTA must implement. Agencies and contractors who already document against 800-53 have most of the control text written.
Zero Trust vs ISO 27001. ISO/IEC 27001 covers information security management broadly. ZTA is one design choice within Annex A, particularly A.5 (organizational controls), A.8 (technological controls), and A.5.15 (access control). ISO 27001 does not require Zero Trust.
Zero Trust vs ZTNA. ZTNA is a product category. Zero Trust is the architecture. ZTNA replaces or augments VPN by giving identity-aware, application-level access without exposing the network. Deploying ZTNA without addressing identity, device, application, and data pillars produces a more granular VPN, not Zero Trust.
Zero Trust for different organization types
SaaS companies. Greenfield environments have the easiest path. Identity is cloud-native, the application portfolio is mostly SaaS with SSO and SCIM, and production supports service mesh and workload identity. The hardest part is usually privileged access to production. SaaS programs hit Advanced maturity on identity and applications within 12 months; data classification and device posture lag.
Enterprises with legacy data centers. The cost is in the network and application pillars. Microsegmenting a 20-year-old data center is expensive, slow, and politically painful. Scope Zero Trust to the cloud and modern apps first, then expand backward as legacy systems retire. The DoD reference architecture accepts a multi-year transition.
Healthcare. HIPAA does not require Zero Trust, but the Security Rule's access, audit, and integrity requirements map cleanly to ZTA capabilities. Most healthcare programs start with privileged access to electronic health records.
Federal agencies and contractors. Zero Trust is no longer optional. The federal executive order and OMB M-22-09 set deadlines that have largely passed. Contractors handling CUI must align with NIST SP 800-171, and CMMC Level 2 assessments include Zero Trust-aligned expectations.
SMBs and startups. Below 250 employees, full Zero Trust is overkill. The pragmatic version: phishing-resistant MFA, an IdP with SSO to every SaaS app, EDR on every endpoint, ZTNA in place of VPN, and a written policy that says no implicit trust based on network location. That is 80% of the benefit at 10% of the cost. Build a compliance program on top once the foundation is in place.
Common pitfalls (and how to avoid them)

Treating Zero Trust as a product purchase. Vendors sell Zero Trust like it is a SKU. Buying a ZTNA platform and declaring victory leaves the device, application, and data pillars unaddressed. Start with an architecture document, not an RFP.
Skipping the protect surface exercise. Teams that try to do Zero Trust to "everything" never finish. Start with the small set of resources where access matters most. Expand later.
Failing to consolidate signals. Zero Trust depends on the Policy Engine seeing identity, device, behavior, and threat signals together. Most enterprises run those in silos. Signal integration is often 30% of the program cost and the part most consistently underestimated.
Killing VPN too fast. ZTNA replaces VPN for application access, not for legacy network access (broadcast, multicast, specialized protocols). Plan for a 24-month parallel run. Retire VPN at 12 months and you reinstall it for the long tail.
Ignoring the operations cost. A Policy Engine that denies the wrong request silently is worse than no Policy Engine. Budget a deny-decision review queue, a fast escalation path, and dashboards. At least 1 FTE per 5,000 employees in steady state.
Forgetting the data pillar. Most rollouts get identity, devices, and networks right. Data classification, DLP, and rights management consistently lag. The optimal end state requires access decisions to include data sensitivity, which requires tagging at scale.
Tools and platforms for Zero Trust
The Zero Trust tooling market is fragmented because the architecture spans five pillars. No single vendor credibly covers all five. The pragmatic approach is a stack of best-of-breed tools, integrated through a Policy Engine that consumes their signals.
| Pillar | Common platforms | What to evaluate |
|---|---|---|
| Identity | Okta, Microsoft Entra ID, Ping Identity, CyberArk (PAM), BeyondTrust (PAM) | Phishing-resistant MFA support, fine-grained authorization, signal export to PE |
| Devices | CrowdStrike, SentinelOne, Microsoft Defender, Jamf, Intune | Posture API quality, integration with IdP for conditional access |
| Networks (ZTNA) | Zscaler ZPA, Cloudflare Access, Netskope, Palo Alto Prisma Access, Cisco Duo Network Gateway, Tailscale, Twingate | Application coverage, agentless options, identity broker support |
| Networks (microsegmentation) | Illumio, Akamai Guardicore, VMware NSX, native cloud (AWS Security Groups, Azure NSG) | East-west visibility, policy authoring, performance impact |
| Applications and workloads | HashiCorp Boundary, SPIFFE/SPIRE, Istio, Linkerd, AWS IAM Roles Anywhere | Workload identity, mTLS at scale, secrets rotation |
| Data | Microsoft Purview, Varonis, Forcepoint DLP, Symantec DLP, Concentric AI | Classification accuracy, integration with access decisions, encryption key management |
Credible Zero Trust outcomes typically run 6 to 12 distinct tools across these pillars, glued together through an IdP that acts as the central Policy Engine and a SIEM or analytics platform that collects telemetry. The integration work, not the tool purchase, is the real program cost.
For the GRC platforms that wrap around Zero Trust programs, see our cybersecurity compliance guide. For the deeper federal-standard view, see the NIST 800-207 implementation guide.
Frequently Asked Questions
What are the five pillars of Zero Trust architecture?
The five pillars come from the CISA Zero Trust Maturity Model: Identity, Devices, Networks, Applications and Workloads, and Data. Two cross-cutting capabilities, Visibility and Analytics and Automation and Orchestration, support all five. Each pillar is scored across four maturity stages (Traditional, Initial, Advanced, Optimal), and a credible Zero Trust program advances across all five pillars in parallel rather than perfecting one before starting the next.
What is the NIST standard for Zero Trust architecture?
NIST SP 800-207, published in August 2020, is the authoritative federal standard. It defines Zero Trust Architecture, lists seven tenets, describes the logical components (Policy Engine, Policy Administrator, Policy Enforcement Point), and outlines deployment variants. NIST SP 1800-35 provides practical implementation guidance with vendor-validated build examples.
What are the three components of Zero Trust architecture?
The Policy Engine decides whether to grant access based on policy and signals. The Policy Administrator establishes or shuts down the communication path between the requester and the resource. The Policy Enforcement Point sits in front of the resource and either passes or blocks traffic. All three are logical roles; in practice they are often combined into one product but the architectural separation matters for clarity and for understanding what the vendor is actually selling you.
Is ZTNA replacing VPN?
For most application access use cases, yes. ZTNA gives users access to specific applications rather than to a network segment, which limits lateral movement and aligns with the per-resource access principle in NIST 800-207. For legacy use cases that genuinely need network-level access, broadcast protocols, specialized industrial systems, certain telephony, VPN persists. The typical enterprise pattern in 2026 is ZTNA for 90% of access, retained VPN for the 10% edge cases.
How long does a Zero Trust rollout take?
Realistically, 18 to 36 months to reach Advanced maturity across the five CISA pillars at a 2,000-employee company. Smaller cloud-native companies can hit Advanced in 12 months because they have less legacy to retire. Large enterprises with extensive on-premises footprint plan for 3 to 5 years. Optimal maturity is a long-term aspiration; very few commercial organizations actually reach it.
Does Zero Trust require microsegmentation?
Not strictly. NIST 800-207 does not mandate any specific technology. Microsegmentation is one way to implement the network pillar; identity-based ZTNA is another. Most mature deployments combine both: ZTNA for user-to-application access, microsegmentation for east-west workload-to-workload traffic. Skipping segmentation entirely leaves lateral movement on the table inside the network, which violates the per-resource access tenet.
How much does Zero Trust cost?
For a mid-market enterprise (around 2,000 employees), expect $1.5M to $4M in year one and $1M to $2.5M annually in steady state. The cost varies by how much identity, EDR, and network tooling is already in place and how much legacy network architecture has to be segmented. The largest hidden cost is integration: getting signals from the device, identity, and network tools into a single Policy Engine that can make real-time decisions.
Bottom line
Zero Trust is not a product, a vendor, or a project with an end date. It is an operating model that assumes every request is untrusted until proven otherwise, every session is reauthorized, and every resource has a policy in front of it. The federal standard is NIST SP 800-207, the operational path is the CISA Maturity Model, and the controls map cleanly to NIST 800-53.
For most enterprises, the right move is phased: start with identity and device posture in months 1 to 9, deploy ZTNA against the top applications in months 6 to 12, then expand into microsegmentation and the data pillar over months 12 to 24. Budget $1.5M to $4M for year one and accept that signal integration, not tool selection, is the real work.
Treat Zero Trust as a vendor purchase and you get a more expensive perimeter. Treat it as an architecture, scoped to a protect surface and operated as a real function, and you get a security posture that matches how you actually work in 2026.
Primary Sources
This article references the following authoritative sources:
- NIST SP 800-207: Zero Trust Architecture. The federal definition, seven tenets, and logical components.
- CISA Zero Trust Maturity Model v2.0. Five-pillar phased model with maturity-stage indicators.
- NIST SP 800-53 Rev 5. Control catalog that operationalizes most ZTA capabilities.
- NIST Cybersecurity Framework 2.0. Risk management framework that Zero Trust supports within the Protect function.
- NIST SP 800-171 Rev 3. Controlled Unclassified Information controls relevant to federal contractors.
- OMB Memorandum M-22-09: Federal Zero Trust Strategy. Federal agency mandate and pillar definitions.
- Executive Order 14028: Improving the Nation's Cybersecurity. The 2021 order that put Zero Trust on the federal agenda.
- NIST SP 1800-35: Implementing a Zero Trust Architecture. Practical, vendor-validated implementation guidance.