What is SOC 2 Type 2? Everything You Need to Know
SOC 2 Type 2 is an independent audit report that verifies whether a service organization's security controls were operating effectively over a defined observation period, typically 3 to 12 months. It is the gold standard security credential for B2B SaaS companies in North America. If your enterprise prospects are asking for "your SOC 2," they almost certainly mean a Type 2 report, not a Type 1.
Understanding the difference matters because they represent very different levels of assurance, and confusing them in a sales conversation will not end well.
SOC 2 Type 1 vs Type 2: The Real Difference
A SOC 2 Type 1 report confirms that your controls were suitably designed at a single point in time. A SOC 2 Type 2 report confirms that those controls were both suitably designed and operating effectively over a period of time.
Think of it this way: Type 1 is a photograph. Type 2 is a 6-to-12-month surveillance video.
An auditor producing a Type 1 report reviews your policies, system descriptions, and control documentation on a specific date and attests that everything appears to be in order. They are not testing whether the controls actually ran consistently. They are testing design.
A Type 2 auditor does all of that, plus collects and tests evidence that your controls functioned throughout the observation period. They sample your access reviews, pull your change management records, review your incident logs, test whether terminated employee accounts were actually disabled on time, and verify that your monitoring alerts fired when they should have.
This is why Type 2 carries significantly more weight with enterprise security teams. It is substantially harder to fake and meaningfully harder to achieve.
The Five Trust Service Criteria
SOC 2 audits are structured around the AICPA's Trust Service Criteria (TSC). Security (Common Criteria) is the only mandatory category. The others are optional add-ons based on what is relevant to your service.
Security (Common Criteria): Controls around logical and physical access, change management, risk management, monitoring, and incident response. Required for every SOC 2 report.
Availability: Controls ensuring your service meets agreed uptime commitments. Relevant for infrastructure providers and SaaS products with availability SLAs.
Processing Integrity: Controls verifying that system processing is complete, valid, accurate, and authorized. Relevant for payment processors, data pipelines, and order management systems.
Confidentiality: Controls protecting information designated as confidential. Relevant when you handle sensitive customer data beyond standard security requirements.
Privacy: Controls over the collection, use, retention, disclosure, and disposal of personal information. Relevant if your service collects and manages significant volumes of personal data.
Most SaaS companies start with Security only, and add Availability if their uptime track record and monitoring infrastructure can support it. Adding unnecessary categories increases audit scope and cost without proportional customer benefit.
What the Observation Period Looks Like
The observation period is the window of time over which your controls are evaluated for Type 2. It typically runs 3 to 12 months, with 6 months being the most common for a first SOC 2 and 12 months being standard for renewals.
During this period, your controls must actually run as documented. This means:
- Access reviews must happen on the schedule your policy specifies
- Security training must be completed by employees within the defined timeframe
- Vulnerability scans must run on schedule and findings must be tracked
- Change management processes must be followed consistently
- Incident response procedures must be followed if any incidents occur
- Background checks must run before new employees access production systems
Evidence of each control is collected automatically by your compliance platform or manually gathered before the audit closes. Auditors then sample that evidence to verify it.
A three-month observation period is faster to complete but provides less assurance in the eyes of enterprise buyers. Some companies specifically require a report covering at least six months. If you are targeting large enterprise customers, start your observation period with a 12-month window in mind.
What Auditors Actually Test
Auditors do not just read your policies and take your word for it. They test. Here is what the testing actually looks like for common controls.
Logical access control: Auditors request a list of all users with access to your production environment and key systems. They select a sample and verify that each person's access was properly provisioned, matches their current role, and was reviewed at the required intervals. They also look at terminated employee accounts and verify access was removed promptly.
Change management: Auditors sample your code deployments, infrastructure changes, and configuration changes over the observation period. They verify that each change followed your defined process, including peer review, testing, and approval before deployment.
Incident management: If you had security incidents during the observation period, auditors review whether they were handled according to your documented procedures, whether they were logged, and whether root cause analysis was performed.
Vendor management: Auditors review your vendor list and check whether you have business associate agreements or vendor contracts with appropriate security terms for your critical third-party providers.
Security monitoring and alerting: Auditors verify that your monitoring tools were running and that alerts were responded to within defined timeframes.
Encryption: Auditors verify that data in transit and at rest is encrypted using acceptable standards.
How to Prepare for a SOC 2 Type 2 Audit
Preparation falls into three phases: readiness, observation, and audit.
Readiness (before the observation period starts): This is where you close control gaps. Conduct a gap assessment against the Trust Service Criteria, document your systems and data flows, write your policies and procedures, implement any missing technical controls, and get your compliance platform in place. Do not start the observation period until your controls are actually running. Auditors will find gaps in your evidence if you start the clock before you are ready.
Observation period: Run your controls consistently and collect evidence continuously. Do not let access reviews slip. Do not let security training completion rates fall. If an incident occurs, follow your procedure and document everything. Think of this period as a test run where every action leaves a paper trail.
Audit fieldwork: Your auditor will request a population of evidence (for example, "all production deployments from the observation period") and then select a sample to test. Respond promptly to requests and provide clean, organized evidence. Disorganized or late responses extend audit timelines and increase costs.
Common Control Failures That Delay or Qualify Reports
A qualified audit report means your auditor found exceptions, which means controls did not operate as described during the observation period. This is something you want to avoid before distributing a report to customers.
Access review failures are the most common reason for exceptions. Many companies define monthly or quarterly access reviews in their policies but fail to actually run them on schedule. Auditors will find the gaps in the evidence.
Terminated employee access not removed promptly. Most policies state access should be removed within 24 hours of termination. Auditors sample terminations during the observation period. Even one instance of delayed removal can generate an exception.
Vulnerability findings not remediated within policy timeframes. If your policy states that critical vulnerabilities are patched within 30 days and you have open critical findings older than that, expect an exception.
Monitoring alerts not acted on. If your SIEM fired alerts that were not acknowledged or documented as reviewed, auditors will flag this.
Change management process bypassed. Emergency deployments or "hotfixes" that skipped peer review or change approval are frequently cited exceptions. Document emergency change procedures in advance and follow them.
Vendor assessments not completed. If your policy requires annual vendor security reviews and you have not completed them for key vendors, this is a common exception in initial Type 2 reports.
Timeline from Start to Report
Here is a realistic timeline for a first SOC 2 Type 2 engagement.
Weeks 1 to 4: Readiness assessment. Gap assessment against the TSC, identification of control gaps, remediation planning.
Weeks 4 to 12: Remediation and implementation. Close control gaps, write or update policies, implement technical controls, deploy and configure your compliance platform.
Months 3 to 9: Observation period. Run controls consistently, collect evidence. Minimum 3 months; 6 months recommended for first reports.
Weeks 1 to 4 of audit: Fieldwork. Auditor requests evidence populations and samples. Your team responds to information requests.
Weeks 4 to 6 of audit: Review and reporting. Auditor reviews evidence, raises any findings, issues draft report for management response, finalizes report.
Total elapsed time from project start to signed report: 9 to 16 months for a 6-month observation period. 6 to 10 months if you rush a 3-month observation period with heavy consultant support.
The fastest credible path to a first SOC 2 Type 2 with a 3-month observation period and a well-prepared team is approximately 6 months. Anything faster should be viewed skeptically.
Distributing Your Report
SOC 2 reports are confidential. They contain detailed descriptions of your control environment, which could be used by an attacker to identify gaps. You should not post your report publicly.
Standard practice is to share the report under a Non-Disclosure Agreement (NDA) with prospects and customers who request it. Most enterprise security teams will sign a mutual NDA. Some companies share only the management summary section, though sophisticated buyers will ask for the full report including the auditor's testing procedures and results.
Your compliance platform will typically generate a security page or trust portal where customers can request access to your report, automate NDA signing, and track who has viewed it.
Frequently Asked Questions
How much does a SOC 2 Type 2 audit cost?
Audit fees from accredited CPA firms typically run $15,000 to $35,000 for a startup or small company and $30,000 to $80,000 for mid-size companies. Add compliance platform costs ($10,000 to $25,000 per year), any consultant fees ($15,000 to $50,000 for first-time implementations), and internal staff time. Total first-year cost for a 50-person company is typically $50,000 to $120,000. Annual renewal audits are less expensive because the foundational evidence collection and policy work is already done.
Can a SOC 2 Type 1 report satisfy enterprise security questionnaires?
Sometimes, but less often than it used to. As of 2026, most enterprise security teams specifically request a Type 2 report. Some will accept a Type 1 if you are in the process of your Type 2 observation period and can provide a clear timeline for when the Type 2 will be available. Using a Type 1 as a permanent substitute will raise flags with experienced buyers.
Do we need to repeat the full audit every year?
Yes, but renewal audits are less intensive than initial audits. Annual renewal covers the most recent 12-month period. Because your auditor already understands your control environment, fieldwork is typically faster and fees are lower. The observation period for renewal reports is usually 12 months, so the clock starts as soon as your previous observation period ends.
What is the difference between a SOC 2 report and SOC 2 certification?
Technically, there is no such thing as SOC 2 certification. SOC 2 is an attestation, meaning an independent CPA attests to your controls. It is not a certification like ISO 27001, which is issued by an accreditation body. When companies say they are "SOC 2 certified," they mean they have a clean SOC 2 Type 2 report. This distinction matters when customers ask whether your report is current, because attestations cover a specific time period and must be renewed annually to remain meaningful.
Which Trust Service Criteria should we include in our first audit?
Start with Security (Common Criteria) only. It is the universal baseline and the category every customer expects. Adding Availability is worth considering if your product is infrastructure, has strict uptime SLAs, or if your target customers have asked for it explicitly. Adding Processing Integrity, Confidentiality, or Privacy increases audit scope and cost meaningfully. Evaluate whether your customers have specifically requested these categories before including them. You can always add categories in a future report period without starting over.
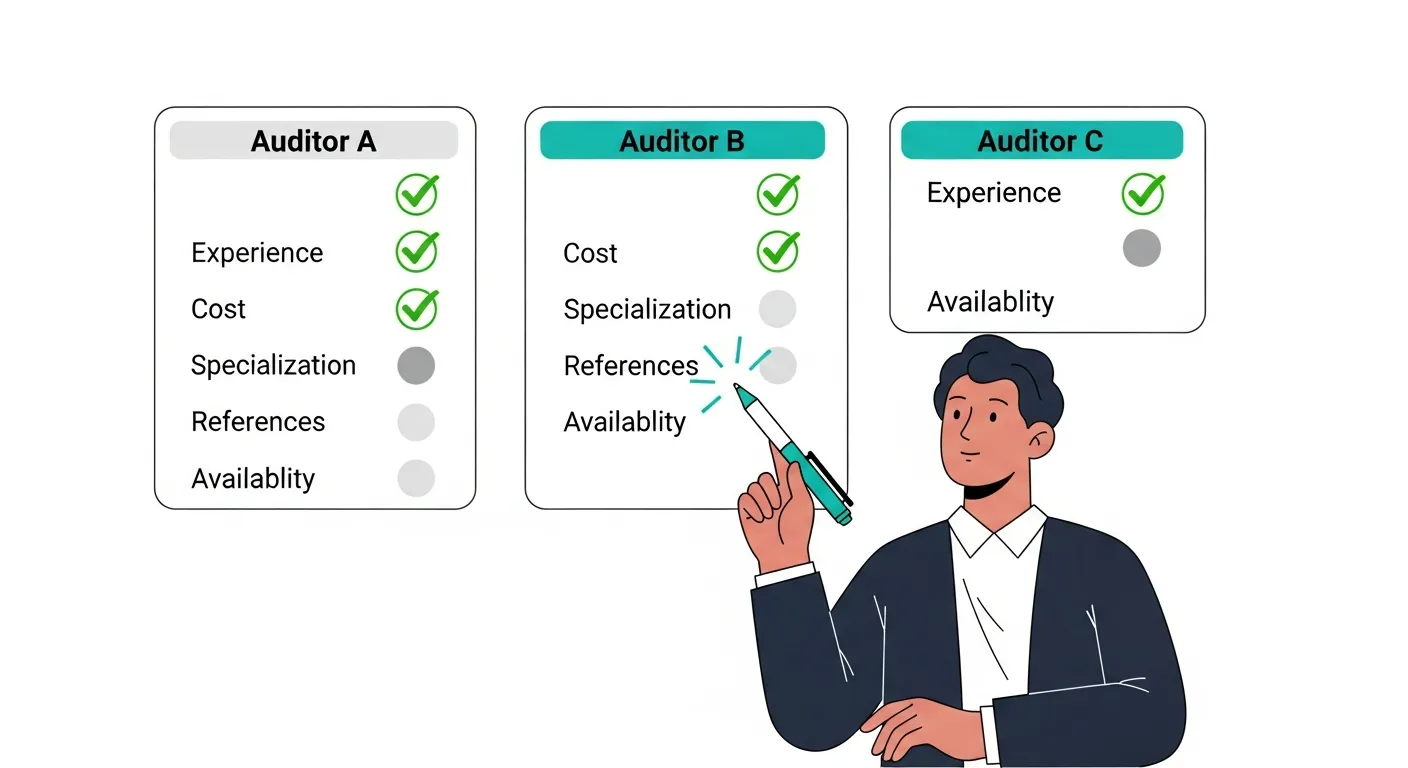
For a step-by-step implementation path, see The Complete SOC 2 Compliance Checklist for 2026. When you are ready to select an audit firm, How to Choose a SOC 2 Audit Firm walks through what separates good firms from bad ones.