Zero Trust Architecture: NIST 800-207 Implementation Guide
Zero trust architecture has moved from buzzword to baseline requirement. According to Gartner, 10% of large enterprises will have a mature zero trust program by 2026, up from less than 1% in 2023. NIST Special Publication 800-207 provides the definitive framework for implementing zero trust. Federal agencies must adopt it under Executive Order 14028. But zero trust is not just a government concern. Startups, SaaS companies, and SMBs handling sensitive data all benefit from understanding NIST 800-207. Whether you are pursuing SOC 2 compliance or operating in a hybrid cloud environment, this standard matters.
This guide breaks down the core principles, deployment models, and practical steps for building a zero trust architecture aligned with NIST 800-207.
What Is Zero Trust Architecture?
Zero trust is a security model built on one principle: never trust, always verify. Traditional network security assumed that anything inside the perimeter was safe. Zero trust assumes that every request, whether from inside or outside the network, could be malicious.
NIST 800-207 defines zero trust architecture (ZTA) as "an enterprise cybersecurity plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies." Published in August 2020, it remains the most widely referenced standard for ZTA implementation. A 2024 Forrester survey found that 72% of organizations are either implementing or planning to implement zero trust.
The key shift is moving access decisions from the network layer to the identity and context layer. Instead of asking "is this user on our network?" zero trust asks three questions. Is this user who they claim to be? Is their device healthy? Should they access this specific resource right now?
The Seven Tenets of NIST 800-207
NIST defines seven foundational tenets for zero trust:
1. All data sources and computing services are considered resources. This includes SaaS applications, IoT devices, employee-owned devices, and cloud workloads. If it processes or stores data, it is a resource that needs protection.
2. All communication is secured regardless of network location. Traffic on the internal network gets the same scrutiny as traffic from the public internet. Encryption and authentication are required everywhere.
3. Access to individual enterprise resources is granted on a per-session basis. Each access request is evaluated independently. Having access to one resource does not automatically grant access to another.
4. Access is determined by dynamic policy. Policies consider the identity of the user, the state of the requesting device, behavioral attributes, and environmental conditions. Static rules based on IP ranges or VLANs are insufficient.
5. The enterprise monitors and measures the integrity and security posture of all owned and associated assets. Devices are continuously assessed. A laptop that was compliant yesterday might not be compliant today if it missed a patch.
6. All resource authentication and authorization are dynamic and strictly enforced before access is allowed. Authentication happens before every access attempt, not just at login. Session tokens must be time-limited and re-evaluated.
7. The enterprise collects as much information as possible about the current state of assets, network infrastructure, and communications. This data feeds into the policy engine and improves security posture over time.
Zero Trust Architecture Components
NIST 800-207 defines three core logical components that make up a zero trust architecture:
Policy Engine (PE)
The policy engine is the brain of zero trust. It makes the ultimate decision to grant, deny, or revoke access to a resource. The PE uses enterprise policy, external data sources (threat intelligence, SIEM data), and the current request context to make decisions.
Policy Administrator (PA)
The policy administrator executes the decisions made by the policy engine. It establishes and shuts down communication paths between the subject (user or device) and the resource. Think of it as the enforcer that tells the network infrastructure what to allow.
Policy Enforcement Point (PEP)
The policy enforcement point is the gateway that enables, monitors, and terminates connections. It is the closest component to the actual resource and user. Every request passes through the PEP, which checks with the PA before allowing traffic.
Three Deployment Models in NIST 800-207
NIST outlines three primary approaches to deploying zero trust:
1. Enhanced Identity Governance
This model centers on strong identity verification and access policies. It works well for organizations that already have mature identity and access management (IAM) systems. The identity provider becomes the primary policy engine, and access decisions are based on user identity, role, device health, and contextual signals.
Best for: Organizations with strong IAM maturity, cloud-first environments, SaaS-heavy workloads.
2. Micro-Segmentation
This model focuses on placing individual or small groups of resources on their own network segments, protected by gateway devices (PEPs). Network traffic between segments is controlled and monitored, regardless of whether it is "internal."
Best for: Data center environments, organizations with sensitive on-premises workloads, healthcare and financial services.
3. Software-Defined Perimeter (SDP)
Also known as a "network overlay" approach, SDP uses software-based mechanisms to create on-demand, identity-based connectivity between users and resources. The network infrastructure itself becomes invisible to unauthorized users.
Best for: Remote workforce scenarios, multi-cloud environments, organizations replacing traditional VPNs.
| Deployment Model | Primary Focus | Best Use Case | Complexity | |---|---|---|---| | Enhanced Identity Governance | Identity and IAM | Cloud-first, SaaS-heavy | Medium | | Micro-Segmentation | Network isolation | Data centers, regulated industries | High | | Software-Defined Perimeter | Overlay networks | Remote work, multi-cloud | Medium-High |
Most organizations will use a hybrid approach combining elements of all three models based on their specific environment and risk profile.
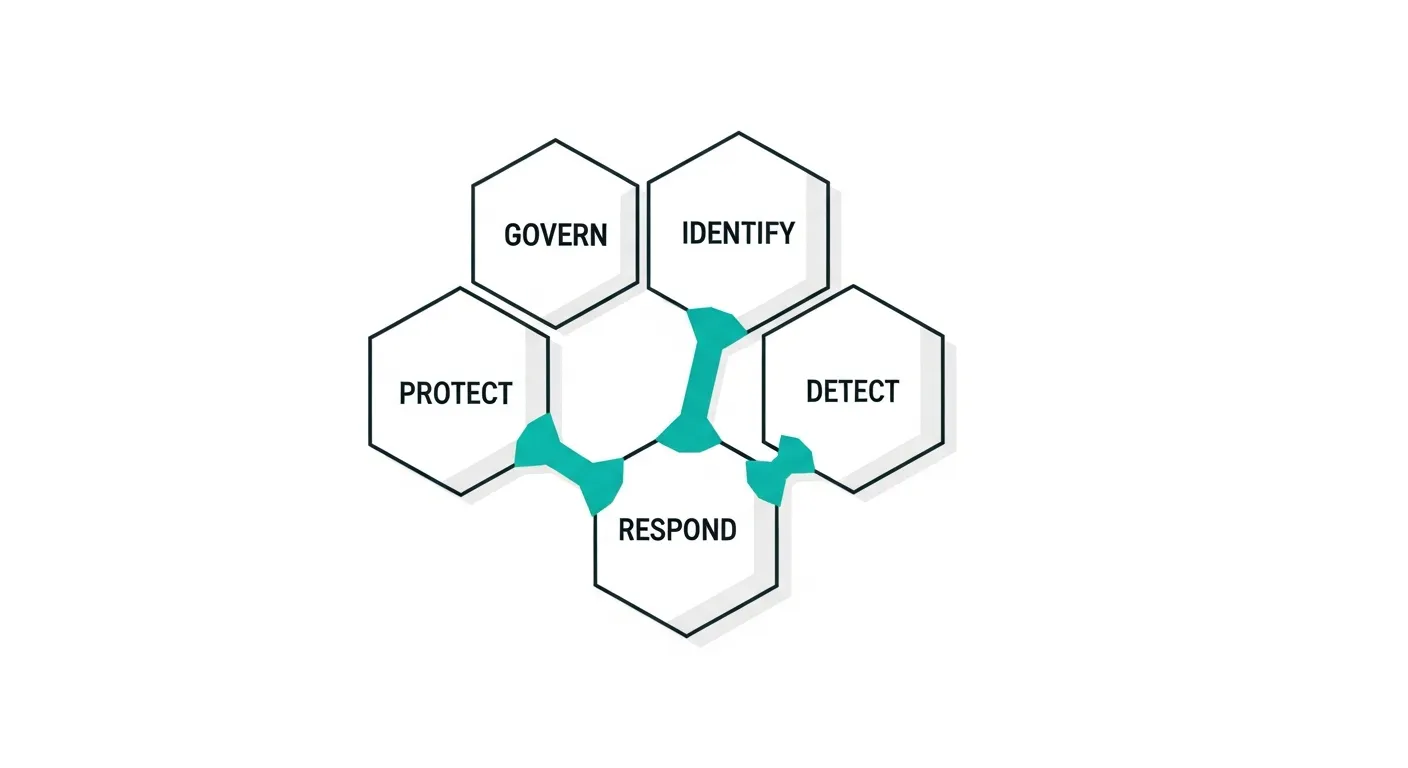
How Zero Trust Maps to Other Compliance Frameworks
Zero trust architecture does not exist in isolation. It directly supports and accelerates compliance with several major frameworks:
NIST 800-53: Zero trust controls map directly to NIST 800-53 families including Access Control (AC), Identification and Authentication (IA), System and Communications Protection (SC), and Audit and Accountability (AU). Organizations implementing NIST 800-53 controls will find significant overlap.
SOC 2: The Trust Service Criteria for security, availability, and confidentiality align naturally with zero trust principles. Continuous monitoring, least-privilege access, and encryption requirements in SOC 2 compliance are all zero trust fundamentals.
HIPAA: Protected health information (PHI) security requirements in HIPAA compliance benefit directly from micro-segmentation and per-session access controls that zero trust provides.
CMMC 2.0: The Department of Defense requires CMMC compliance for defense contractors, and zero trust is a foundational element of Level 2 and Level 3 requirements.
FedRAMP: Federal cloud service providers must demonstrate zero trust capabilities as part of their authorization process.
Step-by-Step Implementation Roadmap

Implementing zero trust is not a weekend project. CISA (Cybersecurity and Infrastructure Security Agency) recommends a phased approach aligned with their Zero Trust Maturity Model:
Phase 1: Assess Your Current State (Weeks 1-4)
- Inventory all users, devices, applications, and data flows
- Map how data moves between systems (both internal and external)
- Identify your most critical assets and data (crown jewels)
- Document existing identity, network, and endpoint security controls
- Baseline your current maturity against the CISA Zero Trust Maturity Model
Phase 2: Define Your Zero Trust Strategy (Weeks 4-8)
- Select your primary deployment model based on your environment
- Define your policy engine requirements and decision criteria
- Establish your identity verification standards (MFA at minimum, phishing-resistant MFA preferred)
- Create a network segmentation plan
- Set measurable milestones and success criteria
Phase 3: Implement Identity Foundation (Weeks 8-16)
- Deploy or strengthen centralized identity provider (Okta, Azure AD, Google Workspace)
- Implement phishing-resistant MFA across all users and applications
- Establish device trust and health verification
- Configure conditional access policies based on user, device, location, and risk
- Integrate identity data with your SIEM for continuous monitoring
Phase 4: Segment and Protect (Weeks 16-24)
- Implement network micro-segmentation around critical assets
- Deploy policy enforcement points at application boundaries
- Enable encryption for all internal and external communications
- Configure least-privilege access for all service accounts
- Implement just-in-time (JIT) access for privileged operations
Phase 5: Monitor and Optimize (Ongoing)
- Deploy continuous monitoring across identity, network, and endpoint layers
- Implement automated threat detection and response
- Conduct regular access reviews and policy audits
- Run tabletop exercises simulating lateral movement scenarios
- Measure progress against CISA maturity model quarterly
Common Zero Trust Implementation Mistakes
Treating it as a product purchase. Vendors will tell you their product "delivers zero trust." No single product does. Zero trust requires orchestration across identity, network, endpoint, and data security layers.
Ignoring legacy systems. Many organizations have legacy applications that cannot support modern authentication. Plan for these early. Use application proxies, API gateways, or network-level controls to wrap legacy systems in zero trust controls.
Skipping the data flow mapping. You cannot protect what you do not understand. Organizations that skip the asset inventory and data flow mapping in Phase 1 invariably create policy gaps that attackers exploit.
Forgetting about service accounts. Human identities get all the attention, but service accounts, API keys, and machine identities often have far more access than any human. Apply the same zero trust principles to non-human identities.
Not measuring progress. Without baselines and metrics, you cannot demonstrate that your zero trust investment is reducing risk. Track metrics like mean time to detect lateral movement, percentage of applications behind PEPs, and MFA adoption rates.
Cost Considerations
Zero trust implementation costs vary widely based on organizational size and existing infrastructure:
| Organization Size | Estimated Cost Range | Timeline | |---|---|---| | Small startup (under 100 employees) | $50,000 to $150,000 | 3-6 months | | Mid-size company (100-1,000 employees) | $200,000 to $750,000 | 6-12 months | | Enterprise (1,000+ employees) | $500,000 to $2,000,000+ | 12-24 months |
These estimates include identity platform costs, network security tools, consulting, and staff training. Startups and SMBs with existing cloud IAM (Google Workspace, Microsoft 365) will be at the lower end. The biggest cost driver for smaller companies is typically the identity platform and MFA rollout, not network hardware.
Frequently Asked Questions
What is NIST 800-207?
NIST Special Publication 800-207 is the U.S. government standard for zero trust architecture. Published in August 2020, it defines the concepts, components, and deployment models for implementing zero trust in enterprise environments.
Is zero trust required by law?
For U.S. federal agencies, yes. Executive Order 14028 (May 2021) mandates zero trust adoption. For private sector organizations, zero trust is not legally required but is increasingly expected by auditors, cyber insurers, and compliance frameworks.
How long does it take to implement zero trust?
A basic zero trust implementation takes 3 to 6 months for small organizations. Enterprise implementations typically take 12 to 24 months. Full maturity across all five pillars (identity, devices, network, applications, data) can take 2 to 3 years.
Can small businesses implement zero trust?
Yes. Small businesses can start with cloud-based identity providers (Google Workspace, Microsoft 365) that include built-in conditional access and MFA. This covers the identity governance deployment model without significant infrastructure investment.
How does zero trust relate to VPNs?
Zero trust replaces the need for traditional VPNs. Instead of tunneling all traffic through a VPN concentrator, zero trust provides per-application access based on identity and device health. This approach is more secure and performs better for remote workers.
What is the CISA Zero Trust Maturity Model?
CISA published a Zero Trust Maturity Model that defines four maturity levels (Traditional, Initial, Advanced, Optimal) across five pillars (Identity, Devices, Networks, Applications and Workloads, Data). Organizations use it to assess their current state and plan improvements.