SOC 2 Report Types: Type I vs Type II Explained
Choosing between a SOC 2 Type I and Type II report is one of the first decisions organizations face when pursuing SOC 2 compliance. The distinction is straightforward: Type I evaluates the design of your controls at a single point in time, while Type II evaluates both the design and operating effectiveness of those controls over a period of typically 3 to 12 months. Understanding which report you need, and when, directly affects your timeline, budget, and how prospects evaluate your security posture.
This guide breaks down both report types, explains the practical differences, and helps you determine which path makes sense for your organization.
What Is a SOC 2 Type I Report?
A SOC 2 Type I report provides a snapshot assessment. An independent CPA firm examines whether your security controls are properly designed and implemented as of a specific date. The auditor reviews your policies, procedures, and technical configurations to confirm they meet the AICPA Trust Service Criteria relevant to your scope.
The key phrase here is "as of." A Type I report dated March 15, 2026, confirms that your controls were suitably designed on that specific day. It says nothing about whether those controls operated consistently before or after that date.
What the auditor evaluates in a Type I:
- Control descriptions: Are your policies documented and do they address each Trust Service Criteria point?
- Implementation evidence: Can you demonstrate that each control exists and is in place (not just on paper)?
- Management assertions: Does your description of the system accurately represent reality?
What Is a SOC 2 Type II Report?
A SOC 2 Type II report goes further. It evaluates both the design and the operating effectiveness of your controls over a defined observation period. That period is usually 3 to 12 months, with 6 months being the most common for first-time audits and 12 months standard for annual renewals.
During the observation period, the auditor collects evidence that your controls are not just designed properly but are actually functioning as intended on an ongoing basis. They sample transactions, review logs, examine access records, and verify that your processes are followed consistently.
What the auditor evaluates in a Type II that differs from Type I:
- Operating effectiveness testing: Did the control work every time it was supposed to during the review period?
- Sample-based evidence: The auditor selects samples (access reviews, change approvals, incident responses) and checks if each was executed according to policy.
- Exception tracking: If a control failed to operate correctly during any sampled instance, the auditor documents it as an exception.
Type I vs Type II: Side-by-Side Comparison
| Aspect | SOC 2 Type I | SOC 2 Type II | |--------|-------------|---------------| | Scope | Control design and implementation | Control design + operating effectiveness | | Time frame | Point-in-time (single date) | Observation period (3-12 months) | | Audit duration | 4-8 weeks | 3-12 months (observation) + 4-8 weeks (reporting) | | Cost | ,000-,000 | ,000-,000+ | | Evidence required | Policies, screenshots, configurations | All of Type I + logs, samples, trend data | | Market acceptance | Acceptable for early-stage companies | Preferred by enterprise buyers | | Repeat cycle | One-time stepping stone | Annual renewal | | Report recipient confidence | Moderate: "Controls exist" | High: "Controls work consistently" |
When to Choose a Type I Report
A Type I report makes sense in specific situations. It is not the weaker option. It is the faster path to demonstrating baseline security maturity.
Choose Type I when:
- You need a report quickly. Enterprise prospects are asking for SOC 2 documentation and you have never been audited. A Type I can be completed in 4 to 8 weeks versus 6 to 12 months for Type II.
- You are building your compliance program for the first time. A Type I validates that your control framework is properly designed before you invest in a full observation period. Think of it as a readiness assessment with a formal attestation attached.
- Your controls are new. If you implemented a new access management system or rebuilt your incident response process in the last 3 months, there is not enough operating history for a Type II. Start with Type I and transition to Type II for the next cycle.
- Stakeholders will accept it. Some prospects, investors, and partners explicitly accept Type I reports, especially from startups and growth-stage companies. Ask before assuming you need Type II.
When to Choose a Type II Report
Type II is the gold standard that enterprise buyers, regulated industries, and security-conscious organizations expect.
Choose Type II when:
- Enterprise customers require it. Most Fortune 500 vendor security questionnaires specifically ask for SOC 2 Type II. A Type I may not satisfy their requirements.
- You are renewing your SOC 2. After your initial Type I (or first Type II), annual renewals should always be Type II. Reverting to Type I signals regression.
- Your controls have 6+ months of operating history. If your security program has been running consistently, skip Type I entirely and go straight to Type II.
- You operate in regulated industries. Healthcare companies handling PHI, financial services firms, and government contractors typically need the stronger assurance that Type II provides, often alongside HIPAA, PCI DSS, or NIST compliance.
The Type I to Type II Transition Path

The most common approach for first-time SOC 2 organizations follows this sequence:
Months 1-2: Readiness Assessment Conduct an internal or consultant-led readiness assessment to identify control gaps. Common findings include missing access review documentation, incomplete risk assessments, and vendor management gaps.
Months 3-4: Type I Audit Engage a CPA firm for the Type I examination. Use the readiness findings to close gaps before the auditor arrives. The Type I validates your control design and gives you a formal report to share with prospects immediately.
Months 5-10: Observation Period Begin the Type II observation window. During these months, your team operates the controls consistently, collects evidence, and resolves any issues. GRC platforms like Vanta, Drata, and Secureframe automate much of this evidence collection.
Months 11-12: Type II Audit The auditor tests operating effectiveness over the observation period. You receive your Type II report, which replaces the Type I as your primary compliance artifact.
Trust Service Criteria Apply to Both Report Types
Both Type I and Type II reports are evaluated against the same Trust Service Criteria defined by the AICPA. The criteria you include in your audit scope determine what the auditor examines.
Security (Common Criteria) is mandatory for every SOC 2 engagement, regardless of report type. The optional categories are:
- Availability: System uptime and performance commitments
- Processing Integrity: Accuracy and completeness of data processing
- Confidentiality: Protection of confidential information
- Privacy: Personal information handling practices
Most organizations include Security, Availability, and Confidentiality. The scope decision is the same whether you pursue Type I or Type II.
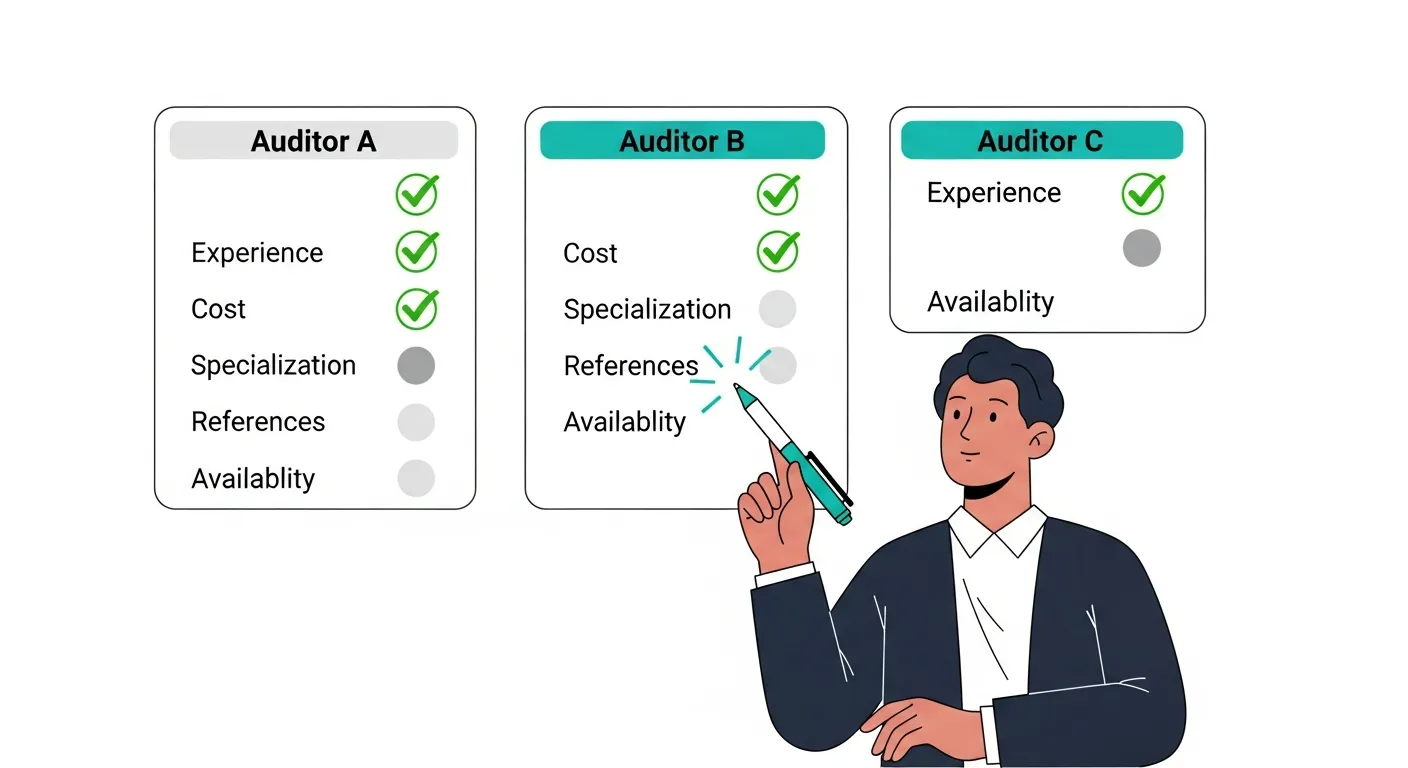
Cost Factors for Each Report Type
Several variables drive the cost difference between Type I and Type II reports:
Auditor fees: Type II requires more testing, sampling, and analysis. Expect 40% to 100% higher auditor fees compared to Type I.
Internal labor: The observation period for Type II requires ongoing evidence collection and control monitoring. Budget 10 to 20 hours per month of internal staff time during the observation window.
GRC platform costs: Most organizations use a compliance automation platform for Type II. Annual costs range from ,000 to ,000+ depending on company size and the platform selected. These tools pay for themselves by reducing audit preparation time and automating evidence collection.
Remediation costs: Type II audits have a higher chance of uncovering operational gaps that require remediation. Budget a contingency of ,000 to ,000 for unexpected fixes during the observation period.
Common Mistakes Organizations Make

Skipping Type I to save money. Organizations that jump straight to Type II without validating their control design often face expensive mid-audit surprises. The Type I investment (even as an informal readiness check) prevents costlier remediation later.
Choosing a 3-month observation period. While 3 months is the minimum for Type II, many enterprise prospects view it skeptically. A 6-month window is the practical minimum for credibility. Annual renewals should cover 12 months.
Letting the Type I expire without transitioning. A Type I report is a stepping stone, not a destination. If 12 months pass without initiating a Type II, prospects may question your commitment to sustained compliance.
Not reading the report before sharing it. SOC 2 reports contain a management assertion section, a description of the system, and the auditor's opinion. Review it carefully for accuracy before distributing. Errors in the system description undermine the report's credibility.
How Prospects Evaluate Your SOC 2 Report
Understanding how buyers read SOC 2 reports helps you choose the right type:
Security teams check the auditor's opinion first. An unqualified (clean) opinion on either report type is the baseline expectation. They then review exceptions and management responses.
Procurement teams look at the report type and coverage period. Type II with a 12-month observation period is the strongest position. Type I is acceptable for new vendors with a stated transition timeline.
Legal teams review the Trust Service Criteria in scope and the system description boundary. They want to confirm that the audit covers the specific services their organization uses.
Frequently Asked Questions
Is a SOC 2 Type I report worthless?
No. A Type I report confirms that your controls are properly designed and implemented. It is widely accepted by mid-market buyers and is the standard first step for organizations new to SOC 2. The claim that "only Type II matters" oversimplifies how buyers actually evaluate vendor security.
Can I go straight to Type II without a Type I?
Yes, if your controls have been operating for at least 6 months and you are confident in their consistency. Some organizations with mature security programs skip Type I entirely. However, a readiness assessment is still recommended before any first-time audit.
How long is a SOC 2 report valid?
Neither Type I nor Type II reports have a formal expiration date. In practice, buyers expect reports to be refreshed annually. A report older than 12 months is considered stale by most enterprise security teams. Some organizations issue a bridge letter between annual reports to address the gap.
Do I need to use the same auditor for Type I and Type II?
No. You can switch CPA firms between engagements. However, using the same firm can be more efficient because they already understand your systems and control environment. If switching, allow extra time for the new auditor's onboarding.
What is a SOC 3 report?
A SOC 3 report is a public-facing summary of a SOC 2 Type II audit. It contains the auditor's opinion but omits the detailed control descriptions and test results. Organizations use SOC 3 reports on their websites as trust badges. You cannot get a SOC 3 without first completing a SOC 2 Type II.