NIST Cybersecurity Framework 2.0: What Changed and What You Need to Do
The NIST cybersecurity framework reached version 2.0 in February 2024, the first major revision since the original 1.0 launched in 2014. The headline change is a new sixth function called Govern, which sits above all the others and addresses organizational context, risk strategy, and supply chain security. If you are still running your program against version 1.1, you are working with a framework that is now two major versions behind.
This article covers every material change, who the framework applies to, how the implementation tiers work, and a practical path for getting started or updating an existing program.
The Six Functions: What They Are and Why Govern Matters
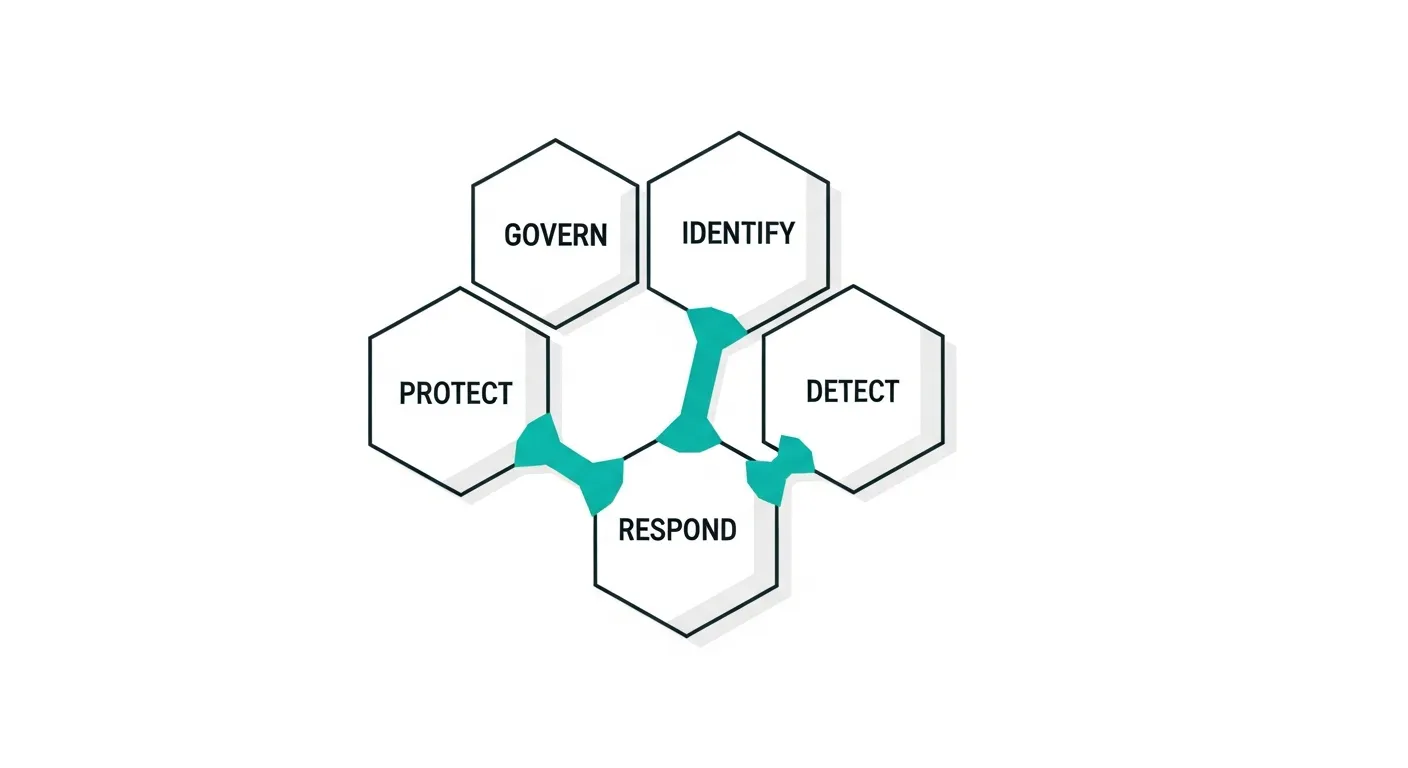
CSF 2.0 organizes cybersecurity activities into six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. Version 1.1 had five functions; Govern is entirely new.
Govern sits at the center of the framework because governance decisions shape everything else. It covers organizational context (what your organization does and why it exists), risk management strategy (how much risk you will accept and how you will prioritize it), roles and responsibilities, policy, oversight, and supply chain risk management. NIST positioned Govern as the function that provides the "why" for all the others.
The other five functions remain conceptually intact from version 1.1, though their subcategories and informative references have been updated.
Identify covers asset management, business environment, risk assessment, and improvement planning. New in 2.0: the Improvement category moves here, pulling in lessons learned and plan updates.
Protect covers identity management, access control, awareness and training, data security, platform security, and technology infrastructure resilience. The categories were reorganized and renamed for clarity.
Detect covers continuous monitoring and adverse event analysis. NIST slimmed this function compared to 1.1, folding some items into Identify.
Respond covers incident management, analysis, mitigation, and reporting. Communication requirements are more explicit in 2.0.
Recover covers incident recovery planning and communication. Largely unchanged from 1.1 in substance.
What Actually Changed from Version 1.1
The Govern function is the biggest structural change, but several other updates matter for practitioners.
Scope expansion. Version 1.1 was written primarily for critical infrastructure operators. NIST explicitly expanded 2.0 to apply to organizations of any size, in any sector, in any country. The framing shifted from "here is a framework for critical infrastructure" to "here is a framework for any organization managing cybersecurity risk."
Supply chain risk management got its own home. NIST added an entire category within Govern dedicated to Cybersecurity Supply Chain Risk Management (C-SCRM). This reflects the reality of software supply chain attacks like SolarWinds and Log4Shell, which exposed how third-party dependencies create systemic risk. The new category includes requirements for understanding dependencies, establishing supplier requirements, and monitoring supplier performance.
The Profiles concept was clarified. CSF 1.1 introduced Current Profiles and Target Profiles but many organizations found the concept confusing. Version 2.0 clarifies that Profiles are simply a way to document your organization's current cybersecurity posture and your desired future state. NIST now provides Community Profiles for specific sectors, which gives you a starting point rather than building from scratch.
Informative references were separated. In 1.1, informative references (mappings to SP 800-53, ISO 27001, CIS Controls, etc.) were embedded in the framework document. In 2.0, NIST moved them to a separate online reference tool. This makes the core document cleaner and allows NIST to update reference mappings without republishing the entire framework.
Measurement got more attention. Version 2.0 includes more explicit guidance on cybersecurity metrics and measurement under the Govern function. The message is that if you cannot measure your program's effectiveness, you cannot manage it.
Who Needs the NIST Cybersecurity Framework
The framework is voluntary for most organizations. Federal agencies are required to use NIST standards under FISMA, and some regulated industries reference it in their own requirements, but there is no general legal mandate forcing private companies to adopt CSF.
That said, several practical pressures push organizations toward it. The SEC's cybersecurity disclosure rules (effective for most public companies in December 2023) require disclosing material cybersecurity incidents and describing cybersecurity risk management processes. Many companies reference the NIST CSF as evidence of a structured risk management process.
Cyber insurance underwriters increasingly ask applicants to demonstrate alignment with recognized frameworks. NIST CSF is one of the most commonly cited. It does not guarantee coverage or lower premiums, but having no framework alignment is increasingly a disqualifier for higher coverage limits.
Federal contractors face the most direct pressure. The Cybersecurity Maturity Model Certification (CMMC) program, which governs defense industrial base contractors handling controlled unclassified information, maps heavily to NIST SP 800-171, which in turn maps to the CSF. Many federal civilian contracts also reference NIST standards in their requirements.
Understanding Implementation Tiers
The NIST CSF implementation tiers describe the degree to which your cybersecurity risk management practices are mature and integrated into your organization. There are four tiers.
Tier 1: Partial. Cybersecurity risk management is ad hoc and reactive. There is no organization-wide policy, practices vary by department, and there is limited awareness of cybersecurity risk at the leadership level. Many small businesses and early-stage companies start here.
Tier 2: Risk Informed. Risk management practices exist but are not formalized as organization-wide policy. Senior leadership is aware of cybersecurity risk but may not have consistent processes for managing it. The organization has some awareness of its cybersecurity dependencies and suppliers.
Tier 3: Repeatable. Formal, documented cybersecurity policies exist. Risk management practices are regularly updated based on changing requirements and threats. The organization can respond consistently to cybersecurity events. Leadership actively participates in risk management decisions.
Tier 4: Adaptive. The organization actively adapts its cybersecurity practices based on lessons learned, threat intelligence, and performance metrics. Cybersecurity is integrated into organizational culture. The organization collaborates with peers to share threat information.
NIST is explicit that Tier 4 is not necessarily the goal for every organization. The appropriate tier depends on your risk tolerance, the sensitivity of your data, your threat environment, and available resources. A small business handling low-sensitivity data may be entirely appropriate at Tier 2.
How to Start or Update Your CSF Program
If you are starting from scratch, the practical sequence is: build your Current Profile, define your Target Profile, conduct a gap assessment, prioritize remediation, and implement.
Step 1: Build your Current Profile. Document what cybersecurity activities you currently perform, mapped to the six CSF functions. Do not document what you aspire to do; document what actually happens today. This is often uncomfortable but essential.
Step 2: Define your Target Profile. Determine what cybersecurity activities you need to perform given your organization's risk tolerance, regulatory requirements, contractual obligations, and threat environment. If you are in a regulated industry, your Target Profile is partly defined by external requirements.
Step 3: Conduct a gap assessment. Compare your Current and Target Profiles. The gaps represent your prioritized work plan. Not every gap carries equal risk; use your risk assessment to sequence remediation.
Step 4: Use the NIST CSF 2.0 reference tool. NIST maintains an online tool at csf.tools (or via the official NIST website) that maps CSF subcategories to SP 800-53, CIS Controls v8, ISO 27001:2022, and other frameworks. If you are already aligned to one of those frameworks, you can map your existing controls to the CSF quickly.
Step 5: Address Govern first if you are updating from 1.1. Most organizations updating from version 1.1 will find their biggest gap in the Govern function, particularly around supply chain risk management and formal risk management strategy documentation. Start there before auditing the other five functions.
If you are already running a mature program against CIS Controls, ISO 27001, or NIST SP 800-53, the effort to align to CSF 2.0 is primarily a documentation and mapping exercise. Your controls likely already address most CSF subcategories. The main additions are formalizing your governance structure and explicitly addressing supply chain risk.
Common Mistakes Organizations Make
The most common error is treating CSF alignment as a checkbox exercise rather than a risk management tool. Organizations that generate a CSF profile to satisfy a questionnaire without actually using it for internal risk decisions get little value from the framework.
The second common mistake is over-scoping the initial effort. NIST designed the framework to be scalable. A 20-person SaaS company does not need the same depth of implementation as a regional bank. Start with the subcategories most relevant to your business and expand over time.
The third mistake is ignoring supply chain. The new Govern function's C-SCRM requirements are the most frequently skipped because they require work that extends beyond your own organization. Start with a simple vendor inventory and a basic third-party risk questionnaire if you do not have a formal program.
Frequently Asked Questions
Is the NIST Cybersecurity Framework mandatory?
For most private companies, no. It is voluntary. Federal agencies are required to use NIST standards under FISMA. Defense contractors handling controlled unclassified information must align to NIST SP 800-171. Some state regulations and industry requirements reference the CSF, so check your specific regulatory environment.
Can I still use NIST CSF 1.1 instead of 2.0?
NIST no longer updates version 1.1. You can technically still reference it, but it lacks the Govern function and the updated supply chain risk management guidance. Auditors, regulators, and cyber insurance underwriters increasingly expect 2.0 alignment. Updating is worth the effort.
How long does CSF 2.0 implementation take?
For an organization with an existing security program, mapping to CSF 2.0 and closing gaps in governance and supply chain risk typically takes 3 to 6 months. Organizations starting from scratch should plan 9 to 18 months to reach Tier 3 maturity, depending on resources and complexity.
Does NIST CSF 2.0 alignment satisfy SOC 2 or ISO 27001 requirements?
Not directly. CSF alignment and SOC 2 or ISO 27001 certifications are separate things. However, they share significant overlap. Organizations aligned to CSF 2.0 at Tier 3 or Tier 4 will find that much of their work translates directly to SOC 2 controls and ISO 27001 clauses, reducing the effort required for those certifications. To understand what those SOC 2 controls actually look like in practice, see The Complete SOC 2 Compliance Checklist for 2026 and our Cybersecurity Compliance Checklist for a cross-framework view.