Incident Response Plan: 2026 Complete Guide
An incident response plan is the written document and operational program that defines how a company detects, contains, eradicates, and recovers from a cybersecurity incident, plus the legal and regulatory disclosures it makes during and after. The federal reference standard is NIST SP 800-61 Rev 2, the Computer Security Incident Handling Guide. The regulatory floor in 2026 is set by the SEC cybersecurity disclosure rules adopted in July 2023, the HIPAA Breach Notification Rule, and CISA advisories.
This guide is for CISOs, security engineers, GRC leads, founders, and counsel who need a single reference for what an IRP must contain in 2026 and how it ties into the broader compliance program. It covers the seven incident handling phases, the SEC 4-business-day Form 8-K clock, the HIPAA 60-day breach notification rule, team roles, severity classifications (P1 through P4), tabletop exercises, ransomware playbooks, and how the plan fits inside a broader cybersecurity compliance program. The companies that handle incident response well treat the plan as a living operational document, not a binder.
What is an incident response plan?
An IRP is a documented set of procedures, roles, and decision criteria that an organization follows when it detects a cybersecurity event. The plan covers technical actions (isolate a host, rotate keys, preserve evidence), governance actions (who declares an incident, who briefs the board), and regulatory actions (when to file an 8-K, when to notify under HIPAA, when to coordinate with the FBI through IC3 and CISA).
NIST SP 800-61 Rev 2 is voluntary but widely adopted, and is what most U.S. regulators implicitly point to when asking whether an organization had a "reasonable" capability. NIST distinguishes between an event (any observable occurrence) and an incident (an event with actual or potential adverse effects on confidentiality, integrity, or availability). Every alert is an event. Only some events are incidents.
An IRP is not a runbook. It is the framework runbooks plug into. A mature program maintains the master IRP plus 8 to 15 playbooks (ransomware, business email compromise, insider exfiltration, denial of service, supply chain, account takeover, cloud key compromise). The master plan governs how playbooks are invoked, who has authority, and what disclosures attach.
Why incident response matters in 2026

Three things have raised the regulatory cost of poor incident response since 2023.
The 2023 SEC cybersecurity disclosure rule. In July 2023, the SEC adopted final rules requiring public companies to disclose material cybersecurity incidents on Form 8-K within four business days of determining materiality, and to disclose risk management, strategy, and governance in the annual 10-K. The clock starts when the company concludes the incident is material, not when it is first detected, which makes the materiality determination itself a control. Companies without a written, repeatable materiality workflow are exposed to enforcement actions for late or inadequate disclosure.
HIPAA Breach Notification enforcement. The HIPAA Breach Notification Rule, enforced by the HHS Office for Civil Rights, requires covered entities to notify affected individuals within 60 days of discovering a breach of unsecured protected health information, notify HHS, and (for breaches affecting 500 or more individuals) notify prominent media in the affected state. See our HIPAA compliance guide for the full stack.
CISA reporting expectations. The Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA) directs CISA to require covered entities to report cyber incidents within 72 hours and ransom payments within 24 hours. As of 2026 the final rule is proceeding through rulemaking. CISA already publishes cybersecurity advisories that organizations are expected to consume and act on.
Two large public breaches have shifted board-level expectations. The SolarWinds supply chain compromise showed that incident response now has to cover third-party code paths. The Equifax data breach showed that the cost of a delayed, poorly-disclosed response is measured in billions, not millions.
Incident response plan requirements
An IRP that satisfies the major U.S. compliance regimes shares a common spine. The components below are required or strongly expected by NIST CSF 2.0, the NIST 800-53 IR control family, the SEC disclosure rule, the HIPAA Security Rule, and PCI DSS 4.0.
| Required Component | What it covers | Driving regulation or standard |
|---|---|---|
| Written, approved plan | Document signed by an executive sponsor, reviewed at least annually | NIST 800-53 IR-1, HIPAA 164.308(a)(6), PCI DSS 12.10.1 |
| Defined incident response team (IRT) | Named roles, primary and backup, with authority to act | NIST 800-61 Section 2.4, NIST CSF Respond function |
| Severity classification | P1 through P4 (or equivalent) with criteria and escalation paths | NIST 800-61 Section 3.2.6 |
| Detection and analysis procedures | How alerts are triaged, who confirms an incident, evidence handling | NIST 800-61 Section 3.2, NIST CSF DE function |
| Containment, eradication, recovery procedures | Decision criteria for short-term vs long-term containment | NIST 800-61 Section 3.3 |
| Materiality determination workflow | How the company decides an incident is material for SEC disclosure | SEC Rule, Form 8-K Item 1.05 |
| Breach notification procedures | Triggers and timelines for HIPAA, state laws, GDPR, contractual | HIPAA 164.404, state breach laws, GDPR Article 33 |
| Communication plan | Internal escalation, external counsel, PR, customers, regulators | NIST 800-61 Section 2.3 |
| Tabletop and exercise schedule | At least annual exercise, post-exercise improvements tracked | NIST 800-53 IR-3, PCI DSS 12.10.2 |
| Lessons-learned process | Post-incident review, root cause, control updates | NIST 800-61 Section 3.4 |
A reasonable IRP in 2026 is not 200 pages. It is a tight 25 to 50 page master document plus the playbooks. Long plans rot. Short, current, exercised plans survive contact with a real incident.
Incident response plan cost and timeline
Costs vary by company size, regulated industry, and whether the team is fully internal, hybrid, or retainer-backed. The figures below are practitioner ranges for U.S. companies in 2026.
Initial plan development (year one). A 30 to 200 person company building its first formal IRP typically spends $25,000 to $80,000 in advisory fees plus 200 to 400 hours of internal time. Larger enterprises can spend $150,000 to $500,000 in year one.
Annual program operating cost. $200,000 to $1.2M annually at the mid-market level, covering a dedicated incident commander, engineer contributions, allocated SIEM and SOAR tooling, retainer fees, and exercise costs.
Incident response retainer. Typical retainers run $15,000 to $50,000 annually for guaranteed response time. Hours convert to fees during an engagement at $400 to $900 per hour. A real ransomware response consumes 800 to 3,000 retainer hours.
Tabletop exercises. $8,000 to $30,000 per facilitated session with a custom scenario. Most regulated organizations run two facilitated and two internal exercises per year.
Timeline. From decision to draft IRP, 8 to 12 weeks. From decision to a tested IRP that can survive an audit, 6 to 9 months. The bottleneck is rarely writing the plan. It is integrating it with the detection stack, training the team, and running the first useful tabletop.
The seven phases of incident response

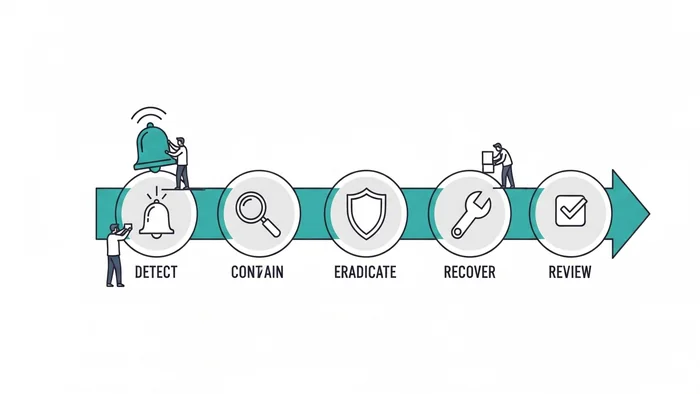
The four-phase NIST 800-61 model and the seven-phase practitioner model describe the same lifecycle at different granularities. The seven-phase version below maps directly into the NIST CSF 2.0 Respond and Recover functions.
1. Preparation. Build the team, write the plan, deploy tooling, train staff, and exercise before an incident occurs. 80% of the value of an IR program lives here. A team that has not exercised will improvise badly on day one.
2. Identification. Detect the event, triage the alert, decide whether it is an incident, classify severity (P1 through P4), and open a formal incident ticket. The output is a written incident declaration with a unique identifier, initial scope estimate, and assigned incident commander.
3. Containment. Short-term containment isolates the immediate threat (disable the account, segment the host, block the C2 domain). Long-term containment puts a sustainable hold on the adversary while the eradication plan is built. NIST 800-61 explicitly warns against jumping straight to eradication because it destroys evidence and often alerts the attacker.
4. Eradication. Remove the adversary and the artifacts. Rebuild compromised systems, rotate all credentials in scope, remove backdoors, patch the initial access vector. Teams often declare victory before they have actually closed the original access path.
5. Recovery. Bring affected systems back into production. Restore from clean backups, validate restored systems are clean before reconnecting them, monitor closely for adversary return. Recovery is also when most disclosure clocks run in parallel, so communications are at peak load.
6. Lessons Learned. Within two weeks of incident close, run a structured post-mortem. Document root cause, timeline, control failures, and a written improvement list with owners and due dates. Track items to closure. This is what turns an incident into a permanent control improvement.
7. Continuous Testing. Annual tabletop minimum. Full-scope red or purple team exercise every 18 months. Update playbooks after every real incident and every exercise. The plan that is not exercised is fiction.
Incident response team roles
A functioning IR team has named roles, not generic responsibilities. NIST 800-61 Section 2.4 outlines the model. The version below reflects how most U.S. mid-market and enterprise companies structure it in 2026.
| Role | Primary responsibility | Who typically fills it |
|---|---|---|
| Incident Commander | Single point of decision authority, runs the incident, owns the timeline | Senior security manager or director, named in advance |
| Technical Lead | Drives the technical response: containment, eradication, recovery actions | Senior security engineer or staff SRE |
| Forensics Lead | Preserves evidence, runs forensic analysis, briefs counsel | In-house DFIR engineer or retainer partner |
| Communications Lead | All internal and external messaging, coordinates with PR and legal | Security PMO, communications team, or external counsel-led |
| Legal Counsel | Privilege, disclosure obligations, law-enforcement coordination | In-house GC or outside counsel |
| Executive Sponsor | Materiality decision, board briefing, sign-off on external disclosure | CFO, COO, or CEO depending on severity |
| Business Owner | Decisions about service impact, customer communication, recovery priorities | Affected business unit leader |
| Scribe | Real-time documentation of decisions, actions, timestamps | Rotating engineer or dedicated analyst |
Every role needs a primary and at least one named backup. Incidents happen on weekends and during the incident commander's vacation. A plan that depends on one person being reachable is broken by definition.
Severity classification: P1, P2, P3, P4
The P1 to P4 model appears in SANS incident handling guidance, most commercial IR retainer SLAs, and NIST 800-61 Section 3.2.6 as one example of a categorization approach.
P1 (Critical). Material business impact, active data exfiltration, production ransomware, or an incident reasonably likely to require SEC disclosure or HIPAA breach notification. Engages the full IRT, executive sponsor, and outside counsel. Response within 30 minutes, 24x7.
P2 (High). Confirmed incident with significant but bounded impact. Includes business email compromise with financial loss, single-host ransomware, privileged account takeover, sensitive data exposure without confirmed exfiltration. Response within 1 hour business, 2 hours off-hours.
P3 (Medium). Contained incident with limited impact. Malware on a single endpoint stopped by EDR, low-volume phishing with confirmed clicks, minor data leakage to a non-adversary recipient. Response within 4 business hours.
P4 (Low). Suspicious activity not rising to a confirmed incident. Investigated, closed, and tracked for trending. Response within one business day.
The severity tier ties directly to the SEC materiality assessment. P1 triggers immediate materiality review by counsel and the executive sponsor. P2 triggers a documented review on a documented timeline. P3 and P4 incidents are not material on their own, but a cluster of P3s may aggregate to a material event.
The SEC 4-business-day disclosure clock

The biggest 2023 to 2026 shift in U.S. corporate incident response is the SEC cybersecurity disclosure rule. The plain reading: a registrant must file a Form 8-K under Item 1.05 within four business days of determining a cybersecurity incident is material.
Two operational points matter.
The clock starts at materiality determination, not detection. The SEC chose this trigger to avoid forcing premature disclosure, but it places the materiality workflow itself inside the disclosure regime. The determination must be made "without unreasonable delay" once facts are known. A plan with no defined workflow, no executive sponsor named to make the call, and no documented timeline is the plan most likely to face an SEC enforcement question.
Form 8-K Item 1.05 content is prescriptive. The filing must describe the material nature, scope, and timing of the incident plus the material impact or reasonably likely material impact. Pre-stage an 8-K template aligned to those elements, reviewed by counsel, so that on day three the company is not drafting from scratch.
The SolarWinds compliance lessons covers what SEC enforcement looks like against companies that disclosed late or incompletely. The pattern is consistent: enforcement focuses less on whether the breach occurred and more on whether the disclosure process was reasonable, repeatable, and timely.
HIPAA breach notification: the 60-day clock
For covered entities and business associates, the HIPAA Breach Notification Rule sets a separate clock. Within 60 calendar days of discovering a breach of unsecured protected health information, the entity must notify each affected individual, notify HHS via the OCR portal, and (for breaches affecting 500 or more individuals in a state) notify prominent media in that state.
The 60-day clock starts at discovery, not materiality determination. Discovery is the first day the breach is known, or by reasonable diligence would have been known, to any workforce member other than the person committing the breach. Both clocks can run simultaneously at a publicly-traded healthcare company. The IRP must handle parallel disclosure timelines without producing inconsistent statements. Counsel coordination is what makes this work.
Ransomware incident response
Ransomware deserves its own playbook. The Target/PCI DSS analysis covers the broader pattern of large breach failure modes. The ransomware-specific elements:
- Do not pay before a structured analysis. OFAC sanctions exposure, the FBI's standing guidance against payment, and the reality that decryptors often fail all argue for a clear-eyed analysis first.
- Engage external IR and counsel within the first hour. Forensics, negotiation, and disclosure all benefit from privileged communication.
- Snapshot evidence before remediation. Encrypted disks, ransom notes, network captures, EDR telemetry. Pre-decide the preservation-vs-recovery tradeoff for each system class.
- Assume data exfiltration. Modern groups exfiltrate before encryption. Treat the incident as a breach unless forensics affirmatively prove otherwise.
- Coordinate with CISA and the FBI. CISA's Stop Ransomware program provides free technical assistance and may identify a known decryptor.
A typical mid-market ransomware response runs 14 to 45 days from detection to recovery, with $500,000 to $5M in incident-related costs separate from any ransom payment.
How incident response fits the broader compliance program
An incident response plan is one chapter of a cybersecurity compliance program. It sits in the Respond and Recover functions of the NIST Cybersecurity Framework but pulls evidence from every other function. Identify feeds the IRP its asset inventory and data classification. Protect controls determine how quickly an adversary can move once inside. Detect is the on-ramp: every alert is the first input to identification. Respond is the IRP itself. Recover covers restoration plus the lessons-learned loop back into Identify and Protect.
For organizations standing up a compliance program from scratch, see our step-by-step build guide. The IRP is usually one of the first three artifacts produced, after the asset inventory and the policy framework.
Common pitfalls
No written materiality workflow. Most companies have an IRP that names a severity scheme but does not say how a P1 escalates into a materiality determination, who makes the call, or what triggers the 8-K filing. This is the single most enforceable gap under the 2023 SEC rule.
The plan and the playbooks disagree. The master IRP says one thing about evidence preservation; the ransomware playbook says another. Adversaries do not care about your version control. Review the plan and playbooks together at least annually.
No backup for every role. Incidents happen on holidays. A plan with single points of failure in human roles fails on day one.
Tabletop exercises that are not exercises. A 90-minute walkthrough with a slide deck is a walkthrough, not an exercise. Real exercises inject ambiguity, time pressure, and contested information. Use external facilitators at least once a year.
No post-incident control updates. Lessons learned without owners, due dates, and tracked closure is a document, not a process. The next incident will notice.
Treating breach notification as a legal-only activity. Notifications to affected individuals, HHS, state AGs, and media are operational workstreams with templates, mailing infrastructure, call center capacity, and identity-protection vendor contracts. They cannot be improvised inside the 60-day clock.
Ignoring third-party scope. The SolarWinds incident and the Equifax incident both involved third-party failure. The IRP should explicitly address what happens when a vendor reports a compromise affecting your systems, and what contractual rights you have to forensic data.
Tools and platforms
The IR tooling stack typically includes a SIEM (Splunk, Microsoft Sentinel, Elastic) for log aggregation; EDR/XDR (CrowdStrike, SentinelOne, Microsoft Defender) for endpoint response; SOAR (Tines, Torq, Splunk SOAR) for playbook automation; case management (TheHive, ServiceNow SecOps); forensics tools (Velociraptor, KAPE); and dedicated war room channels with an out-of-band fallback like Signal.
The platforms do not produce a working IRP. They produce data and automation that a working IRP consumes. Companies that buy tooling without the program discover during their first real P1 that the tools have been ingesting logs nobody reads.
Frequently Asked Questions
What are P1, P2, P3, and P4 incidents?
P1 is a critical incident with material business impact and potential disclosure obligations (production ransomware, confirmed data exfiltration). P2 is a confirmed incident with significant but bounded impact. P3 is a contained, limited-impact incident. P4 is suspicious activity not rising to a confirmed incident. The model aligns with NIST 800-61 Section 3.2.6 examples and most commercial IR retainer SLAs.
What are the 8 basic elements of an incident response plan?
A mission and scope statement, executive sponsor and approval, defined IR team and roles, a severity classification scheme, detection and analysis procedures, containment-eradication-recovery procedures, communication and disclosure procedures, and a post-incident review and exercise program. Each maps to a section of NIST SP 800-61 Rev 2.
What are the 7 stages of incident response?
Preparation, Identification, Containment, Eradication, Recovery, Lessons Learned, and Continuous Testing. The seven-stage model is a granular restatement of the four-phase NIST 800-61 lifecycle and is compatible with the NIST CSF 2.0 Respond and Recover functions.
How fast must a public company disclose a cyber incident?
Within four business days of determining the incident is material. The trigger is the materiality determination, not initial detection. The disclosure is filed on Form 8-K under Item 1.05 and must describe the nature, scope, timing, and material impact of the incident. See the SEC final rule.
What is the HIPAA breach notification timeline?
Within 60 calendar days of discovering a breach of unsecured protected health information. Covered entities must notify each affected individual, notify HHS via the OCR portal, and (for breaches of 500 or more individuals in a state) notify prominent media in that state. See the HIPAA Breach Notification Rule.
Do small businesses need an incident response plan?
Yes. State breach notification laws apply at any size, FTC data security expectations apply to any business holding personal information, and cyber insurance underwriters now require a written IRP as a condition of coverage. Small businesses can run a 15 page plan; they cannot run no plan.
How often should we run a tabletop exercise?
At least annually as the absolute minimum, twice a year for regulated companies, and quarterly for critical infrastructure. A reasonable cadence is one external-facilitator tabletop and one internal exercise per year, plus a red or purple team simulation every 18 months.
Bottom line
An IRP in 2026 is the operational program, not the binder: a written master plan, 8 to 15 playbooks, a named team with backups, a documented materiality workflow, and a tested capability to file an 8-K in four business days, notify under HIPAA in 60 days, and brief CISA when ransomware is involved. The companies that handle incidents well exercise the plan, update it after every event, and treat lessons learned as a control improvement engine.
For broader context, see our cybersecurity compliance guide and NIST Cybersecurity Framework guide.
Primary Sources
This article references the following authoritative sources:
- NIST SP 800-61 Rev 2: Computer Security Incident Handling Guide. The federal reference standard for incident handling.
- NIST Cybersecurity Framework 2.0. Respond and Recover functions referenced throughout.
- NIST SP 800-53 Rev 5. Incident Response (IR) control family.
- SEC Final Rule: Cybersecurity Disclosure (2023). Form 8-K Item 1.05 4-business-day disclosure requirement.
- HIPAA Breach Notification Rule. HHS OCR enforcement, 60-day individual notification clock.
- CISA Cybersecurity Advisories. U.S. national baseline for active threats and recommended actions.
- CISA Stop Ransomware. Federal ransomware guidance and resources.
- FBI Internet Crime Complaint Center (IC3). Federal reporting channel for cyber incidents.
- FTC Data Security Guidance. FTC enforcement expectations on data security.