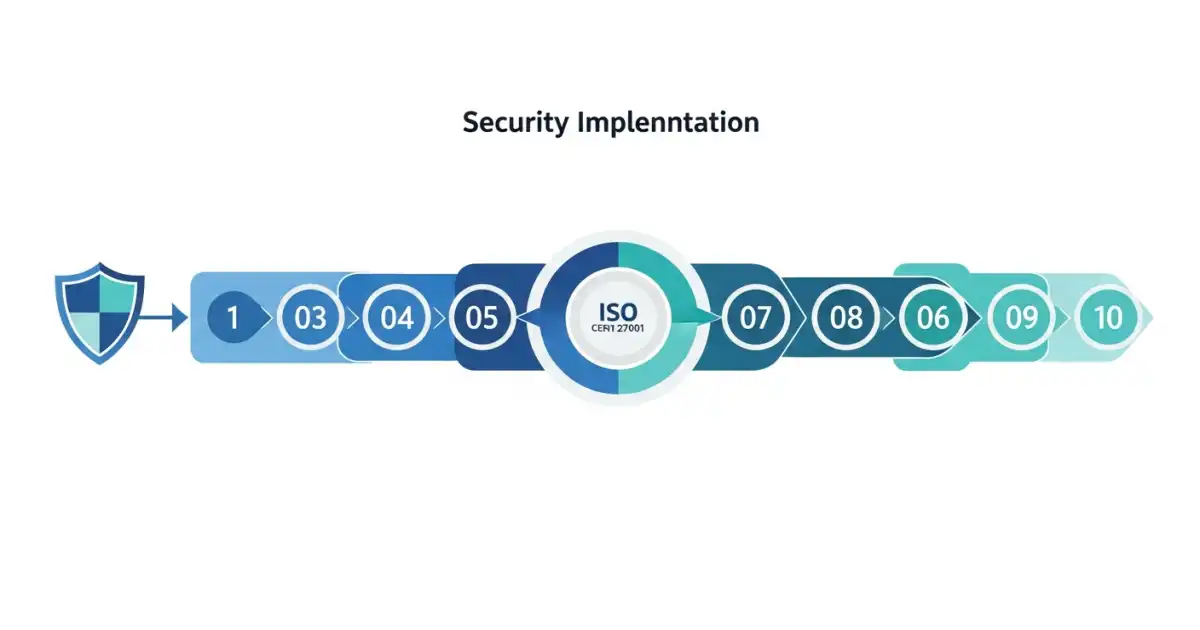
ISO 27001 Certification Process: Step-by-Step Guide
The ISO 27001 certification process follows a structured path from initial scoping through a two-stage external audit. Most organizations complete it in 9 to 18 months, though well-prepared teams with existing security programs can finish in as few as 6 months. The process itself is not complex, but each phase has specific outputs that the certification body auditor expects to see.
This guide covers every step of the ISO 27001 certification process, what auditors look for at each stage, and the common mistakes that delay certification. If you are evaluating costs before starting, see our ISO 27001 certification cost breakdown for detailed budgets by company size.
Step 1: Define the ISMS Scope
Every ISO 27001 implementation begins with a scope statement. This document defines which parts of your organization, which systems, locations, and business processes fall under the Information Security Management System (ISMS).
Getting the scope right is critical because it determines the audit effort, the cost, and the controls you need to implement. A scope that is too broad increases cost and complexity. A scope that is too narrow may not satisfy customer requirements.
What the scope statement must include:
- Organizational boundaries (which departments, teams, or business units)
- Physical boundaries (which offices, data centers, or remote work arrangements)
- Technology boundaries (which systems, networks, cloud environments, and applications)
- Interfaces and dependencies (third parties, outsourced services, shared infrastructure)
- Exclusions with justification (Annex A controls you consider not applicable, with documented reasoning)
A common mistake is scoping the ISMS to "the entire organization" without understanding the implications. For a 200-person company, this means every department, every contractor, and every system is subject to audit. Most organizations benefit from starting with a focused scope tied to their primary product or service.
Step 2: Conduct a Gap Assessment
Before building your ISMS, you need to understand where you stand today. A gap assessment compares your current security posture against the 93 controls in ISO 27001:2022 Annex A and the clauses in the main standard (Clauses 4 through 10).
The gap assessment produces three outputs:
- A control-by-control inventory showing which Annex A controls are already implemented, partially implemented, or missing
- A list of documentation gaps (missing policies, procedures, or records)
- A prioritized remediation plan with estimated effort for each gap
You can perform the gap assessment internally if you have someone who understands the standard well. Most companies hire a consultant for this phase, typically a 2 to 5 day engagement costing $3,000 to $15,000 depending on organizational complexity.
The gap assessment is not a formal audit. No pass/fail result is issued. Its purpose is to create a realistic project plan and budget for the implementation phase.
Step 3: Build the Risk Assessment Framework

ISO 27001 is a risk-based standard. Clause 6.1.2 requires you to define and apply a formal risk assessment process. This is not a one-time exercise but an ongoing methodology your organization commits to using.
Your risk assessment framework must include:
- A risk identification method (how you discover risks)
- A risk analysis method (how you evaluate likelihood and impact)
- Risk acceptance criteria (what level of residual risk is acceptable)
- A risk treatment plan (how you decide to mitigate, transfer, accept, or avoid each risk)
- A risk owner for every identified risk
Most organizations use a 5x5 likelihood-impact matrix with qualitative scales. The specific methodology matters less than consistency. Auditors want to see that you applied the same method across all identified risks and that the results drove your control selection.
The risk register becomes a living document. You will update it as threats change, after incidents, and during management review meetings.
Step 4: Write Policies and Procedures
ISO 27001 requires a minimum set of documented policies and procedures. The 2022 revision reduced the documentation burden compared to the 2013 version, but the following are mandatory:
Required documents:
- Information Security Policy (Clause 5.2)
- ISMS Scope Document (Clause 4.3)
- Risk Assessment Methodology (Clause 6.1.2)
- Risk Treatment Plan (Clause 6.1.3)
- Statement of Applicability (Clause 6.1.3d)
- Information Security Objectives (Clause 6.2)
- Evidence of competence (Clause 7.2)
- Internal Audit Procedure and Results (Clause 9.2)
- Management Review Records (Clause 9.3)
- Corrective Action Records (Clause 10.1)
Commonly needed operational procedures:
- Access Control Policy
- Acceptable Use Policy
- Incident Response Procedure
- Change Management Procedure
- Business Continuity Plan
- Supplier Security Assessment Procedure
- Data Classification and Handling Procedure
- Backup and Recovery Procedure
The total documentation set for a mid-size company typically runs 25 to 40 documents. Quality matters more than quantity. Auditors look for policies that are specific to your organization, not generic templates with your company name swapped in.
Step 5: Implement Controls and Collect Evidence
With policies written and risks identified, you implement the security controls specified in your Statement of Applicability. This is typically the longest phase, consuming 3 to 9 months depending on how many gaps exist.
Implementation priorities should follow your risk assessment. High-risk items with missing controls come first. Common implementation areas include:
- Access management: Implementing role-based access control, multi-factor authentication, regular access reviews, and joiners/movers/leavers processes
- Vulnerability management: Deploying scanning tools, establishing patching cadences, and documenting remediation timelines
- Incident response: Creating response playbooks, defining severity levels, establishing communication channels, and running a tabletop exercise
- Asset management: Building an inventory of information assets, assigning owners, and classifying data
- Supplier management: Assessing third-party security, adding security clauses to contracts, and monitoring ongoing compliance
Evidence collection is just as important as implementation. For every control, you need evidence that it exists, operates as designed, and has been consistently applied. Evidence types include system screenshots, configuration exports, log samples, training attendance records, policy acknowledgment signatures, and meeting minutes.
GRC platforms like Vanta, Drata, or Sprinto automate much of this evidence collection for cloud-based controls by pulling data directly from AWS, Azure, Google Workspace, Okta, and similar services. The ISO 27001 certification process depends heavily on consistent evidence collection throughout the implementation phase, not just at audit time.
Step 6: Conduct Security Awareness Training

Clause 7.3 requires that all persons doing work under the organization's control are aware of the information security policy, their contribution to ISMS effectiveness, and the consequences of not conforming.
In practice, this means:
- All employees complete security awareness training at least annually
- Training covers phishing recognition, password practices, incident reporting, data handling, and physical security
- New hires receive training during onboarding
- Training completion records are maintained as evidence
Auditors check training records during the Stage 2 audit. They may also ask random employees about security policies during walkthroughs to verify that awareness training translates into actual understanding.
Step 7: Run an Internal Audit
Clause 9.2 requires at least one internal audit before the certification audit. The internal audit evaluates whether your ISMS conforms to the ISO 27001 requirements and your own policies.
Internal audit requirements:
- The auditor must be independent (cannot audit their own work)
- The audit must cover all ISMS clauses and applicable Annex A controls
- Findings must be documented, including nonconformities and observations
- A corrective action plan must be created for any nonconformities found
Many companies hire an external consultant to perform the internal audit. This costs $3,000 to $10,000 depending on scope and provides an objective assessment before the certification body arrives.
The internal audit typically reveals 5 to 15 findings in a first-time implementation. These range from minor documentation gaps to procedural inconsistencies. Closing these findings before the certification audit is essential.
Step 8: Conduct a Management Review
Clause 9.3 requires top management to review the ISMS at planned intervals. At least one management review must occur before the certification audit.
The management review must cover:
- Status of actions from previous reviews
- Changes in external and internal issues relevant to the ISMS
- Information security performance (incident metrics, audit findings, objective progress)
- Results of risk assessment and risk treatment plan status
- Opportunities for improvement
The output must include decisions related to continual improvement opportunities and any need for changes to the ISMS. Document the meeting with formal minutes, attendee list, agenda, and decisions made. Auditors will ask to see management review records.
Step 9: Stage 1 Audit (Documentation Review)

The certification audit is split into two stages. Stage 1 is primarily a documentation review conducted by the certification body auditor.
During Stage 1, the auditor evaluates:
- ISMS scope and boundaries
- Information security policy and objectives
- Risk assessment methodology and results
- Statement of Applicability
- Internal audit results and corrective actions
- Management review records
- Readiness for Stage 2
Stage 1 typically takes 1 to 2 days on-site or remotely. The auditor issues a report identifying any areas of concern that must be addressed before Stage 2. There is usually a 4 to 8 week gap between Stage 1 and Stage 2 to allow for remediation.
Step 10: Stage 2 Audit (Implementation Verification)
Stage 2 is the main certification audit. The auditor verifies that your ISMS is implemented, operating effectively, and producing the results described in your documentation.
Stage 2 audit activities include:
- Interviewing staff across departments (IT, engineering, HR, management)
- Reviewing evidence of control operation (logs, tickets, screenshots, records)
- Sampling processes to verify consistency (checking 5 to 10 access reviews, 3 to 5 incident records, etc.)
- Evaluating risk treatment effectiveness
- Verifying corrective actions from Stage 1 and internal audit findings
Stage 2 typically takes 3 to 8 audit days depending on company size. Findings are classified as:
- Major nonconformity: A significant failure in the ISMS that must be corrected before certification can be granted. You typically get 90 days to resolve and submit evidence.
- Minor nonconformity: A less critical issue that must be corrected, usually within 90 days, but does not block certification.
- Observation / opportunity for improvement: A suggestion for enhancement, not a requirement.
Most first-time implementations receive 2 to 5 minor nonconformities, which is normal and expected. Zero findings would be unusual and might indicate an overly surface-level audit.
After Certification: Maintaining Your ISMS
Receiving the ISO 27001 certificate is not the finish line. The three-year certification cycle requires ongoing commitment:
- Year 1 surveillance audit: A focused audit (1 to 3 days) reviewing changes since certification, a sample of controls, and corrective action closure
- Year 2 surveillance audit: Similar scope to Year 1, covering different control areas
- Year 3 recertification audit: A comprehensive audit similar in scope to the original Stage 2
Between audits, you must maintain continuous operations: updating the risk register, collecting evidence, conducting internal audits, running management reviews, and responding to incidents according to your procedures.
Organizations that treat the ISO 27001 certification process as a one-time project rather than an ongoing program struggle significantly at surveillance and recertification audits. For a comparison of how ISO 27001 relates to other frameworks, see our guide on ISO 27001 vs SOC 2 vs NIST.
According to the ISO Survey of Certifications 2023, over 70,000 organizations worldwide hold ISO 27001 certificates, with the number growing approximately 20% year over year since 2020.
Frequently Asked Questions
Q: How long does ISO 27001 certification take from start to finish?
A: Most organizations complete the ISO 27001 certification process in 9 to 18 months. Companies with existing security programs (SOC 2, NIST, or mature internal controls) can often finish in 6 to 9 months. The timeline depends on gap severity, internal resource availability, and certification body scheduling. Stage 1 and Stage 2 audits themselves take 1 to 2 weeks total, but the preparation work drives the overall timeline.
Q: Can a small startup get ISO 27001 certified?
A: Yes. Companies with as few as 5 to 10 employees have successfully achieved certification. The key is keeping the ISMS scope focused. A small SaaS company might scope only its production cloud environment and the development team. With a compliance platform like Sprinto or Drata handling evidence collection and a consultant guiding the implementation, total cost for a small startup typically ranges from $30,000 to $60,000 in the first year.
Q: What is the difference between ISO 27001 Stage 1 and Stage 2 audits?
A: Stage 1 is a documentation review. The auditor checks that your policies, risk assessment, Statement of Applicability, and other required documents exist and meet the standard's requirements. Stage 2 is an implementation audit where the auditor verifies that controls are actually operating as documented through interviews, evidence sampling, and process observation. Both stages must be completed by the same certification body.
Q: What happens if you fail the ISO 27001 audit?
A: You do not technically "fail" the audit. If the auditor finds major nonconformities, certification is not granted until those issues are resolved. You typically have 90 days to implement corrective actions and submit evidence. The auditor then reviews the evidence (sometimes with a follow-up visit) and makes a certification decision. Minor nonconformities do not block certification but must be addressed within the agreed timeframe.
Q: Do we need ISO 27001 if we already have SOC 2?
A: It depends on your market. SOC 2 is predominantly recognized in North America. ISO 27001 carries stronger weight in Europe, the UK, Asia-Pacific, and the Middle East. If you sell internationally, ISO 27001 is often required alongside or instead of SOC 2. The good news is that roughly 60 to 70 percent of SOC 2 controls map to ISO 27001 Annex A controls, so the incremental effort is lower than a greenfield implementation.